Improving the Security of Quantum Protocols via Commit&Open Ivan - - PowerPoint PPT Presentation
Improving the Security of Quantum Protocols via Commit&Open Ivan - - PowerPoint PPT Presentation
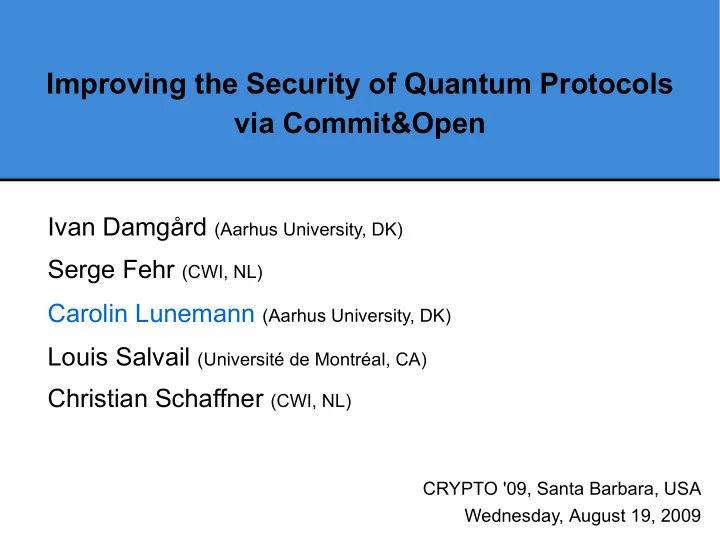
Improving the Security of Quantum Protocols via Commit&Open Ivan Damgrd (Aarhus University, DK) Serge Fehr (CWI, NL) Carolin Lunemann (Aarhus University, DK) Louis Salvail (Universit de Montral, CA) Christian Schaffner (CWI, NL) CRYPTO
Main Results
Benign security against Bob Unconditional security against Alice
π
Commit&Open
(with special properties)
Compiler
BB84-type protocol
Computational security against Bob Unconditional security against Alice
C
α(π) Only constant increase of qubits and rounds Preservation of sequential composability
1 / 20
Benign security against Bob Unconditional security against Alice
π
Commit&Open
(with special properties)
BQSM-security
BB84-type protocol
Computational security against Bob Unconditional security against Alice
C
α(π)
Hybrid security
Main Results
Compiler
Only constant increase of qubits and rounds Preservation of sequential composability
2 / 20
Benign security against Bob Unconditional security against Alice
π
Commit&Open
(with special properties)
Compiler
BB84-type protocol
Computational security against Bob Unconditional security against Alice
C
α(π) Only constant increase of qubits and rounds Preservation of sequential composability
Intuition
3 / 20
preparation (quantum)
1 1
BB84-type protocols
post-processing (classical)
R R 1
arbitrary classical messages and local computations
Intuition | Improvement | Proof Sketch | Results | Summary 4 / 20 Notation: C. Schaffner
preparation (quantum)
1 1
BB84-type protocols
post-processing (classical)
R R 1
arbitrary classical messages and local computations
Intuition | Improvement | Proof Sketch | Results | Summary 5 / 20
- Bob measures in random bases:
- He knows whenever .
- For his uncertainty is high (privacy
amplification).
- We must ensure that Bob measures most of his qubits
before Alice announces further information (e.g. her bases).
Security
Intuition | Improvement | Proof Sketch | Results | Summary 6 / 20
preparation (quantum)
1 1
BB84-type protocols
post-processing (classical)
1 1
arbitrary classical messages and local computations
Intuition | Improvement | Proof Sketch | Results | Summary 7 / 20
- Bob measures in random bases:
- He knows whenever .
- For his uncertainty is high (privacy
amplification).
- We must ensure that Bob measures most of his qubits
before Alice announces further information (e.g. her bases).
- Security against benign Bob ('almost' honest in
preparation phase).
- Unconditional security against dishonest Alice.
Security
Intuition | Improvement | Proof Sketch | Results | Summary 8 / 20
Improvement
Benign security against Bob Unconditional security against Alice
π
Commit&Open
(with special properties) BB84-type protocol
Computational security against Bob Unconditional security against Alice
C
α(π)
Compiler
Only constant increase of qubits and rounds Preservation of sequential composability
9 / 20
Security
post-processing (classical) preparation (quantum)
1 1
verification (classical) arbitrary classical messages and local computations
Intuition | Improvement | Proof Sketch | Results | Summary 10 / 20
Commit&Open
- Idea already in 1-2 QOT [BBCS91].
- Intuition: If Bob passes the measurement test, he must
have measured most of his qubits (also in the remaining subset).
- Partial results for QOT,
e.g. [Yao95, Mayers96, CDMS04].
- Formal characterization of what Commit&Open
achieves in a quantum world B ⇒ enignity
Intuition | Improvement | Proof Sketch | Results | Summary 11 / 20
Commit&Open
⇒ Computational Security
- Commitment can only be computationally binding.
- Standard reduction from computational security of
protocol to computational binding property of commitment would require rewinding.
- Quantum rewinding is only possible in limited settings
[Watrous06].
Intuition | Improvement | Proof Sketch | Results | Summary 12 / 20
- Bob treats the qubits 'almost' honestly in preparation
phase.
- Two conditions are satisfied after preparation phase:
- Bob’s quantum storage is small:
- There exists a , such that the uncertainty about
is (essentially) 1 whenever :
Benignity
for any for any fixed for any ; ; ; ; where
Intuition | Improvement | Proof Sketch | Results | Summary 13 / 20
Computational Security
- Simulation-based proof in the common-reference-
string model.
- Commitment scheme with special properties and secure
against quantum adversaries (e.g. [Regev05]).
- Keyed dual-mode commitment scheme
- Unconditionally binding key pkB.
- Unconditionally hiding key pkH.
- Indistinguishability of keys (also for quantum
algorithms).
Intuition | Improvement | Proof Sketch | Results | Summary 14 / 20
Indistinguishability
- ut[C
α(π)]A,B'
- ut[C
α
pkH(π)]A,B'
- ut[C
α
pkB(π)]A,B'
- ut[π]Ao,B'o
= ≈q =
Intuition | Improvement | Proof Sketch | Results | Summary 15 / 20
Indistinguishability
- ut[C
α(π)]A,B'
- ut[C
α
pkH(π)]A,B'
- ut[C
α
pkB(π)]A,B'
- ut[π]Ao,B'o
= ≈q =
Intuition | Improvement | Proof Sketch | Results | Summary 15 / 20
General Compiler
If the original protocol π is unconditionally secure against a β-benign adversary, then the compiled protocol C
α(π) is (quantum-)
computationally secure against any adversary for const. 0 < α < 1, 0 < β . Unconditional security against Alice is maintained. Main Theorem:
Intuition | Improvement | Proof Sketch | Results | Summary 16 / 20
General Compiler
- Benignity is (relatively) weak assumption.
- Compilation only requires an increase of qubits and
rounds by a constant factor.
- Compilation preserves sequential composability
[FS09].
Intuition | Improvement | Proof Sketch | Results | Summary 17 / 20
Hybrid Security
Benign security against Bob Unconditional security against Alice
π
Commit&Open
(with special properties)
BQSM-security
BB84-type protocol
Computational security against Bob Unconditional security against Alice
C
α(π)
Hybrid security
Compiler
Only constant increase of qubits and rounds Preservation of sequential composability
Intuition | Improvement | Proof Sketch | Results | Summary 18 / 20
Hybrid Security
If π is unconditionally secure against γ -BQSM Bob, then C
α(π) is computationally secure against
a dishonest Bob and unconditionally secure against
γ(1 – α) -BQSM Bob
for const. 0 < α < 1, 0 < γ < 1. Unconditional security against Alice is maintained. Theorem: Bob needs large quantum memory and large quantum computing power.
Intuition | Improvement | Proof Sketch | Results | Summary 19 / 20
Summary
- General compiler to additionally achieve computational
security.
- Characterization of commit&open in quantum settings
(benignity).
- Protocols with hybrid security,
e.g. QOT [BBCS91] and QID [DFSS07].
- Hybrid security against man-in-the-middle attacks
for QID.
- Extensions for noisy quantum communication.
Intuition | Improvement | Proof Sketch | Results | Summary 20 / 20
- Full Version: arXiv: 0902.3918
- Quantum-Secure Coin-Flipping and Applications
(Damgård and Lunemann; to appear at Asiacrypt'09, arXiv: 0903.3118)
- Sampling in a Quantum Population, and Applications