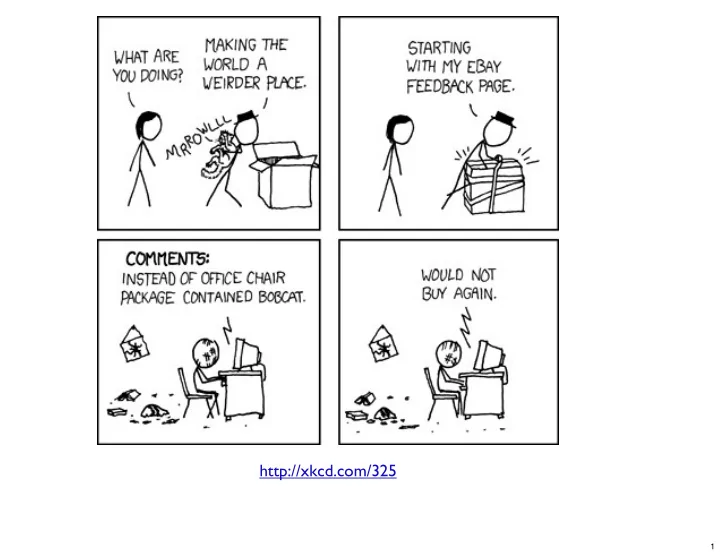
http://xkcd.com/325
1
http://xkcd.com/325 1 Building Useful Security Infrastructure for - - PowerPoint PPT Presentation
http://xkcd.com/325 1 Building Useful Security Infrastructure for Free Now with more Madness!! 2 Who am I? Brad Lhotsky, Recovering Perl Programmer Information Security Manager System Administrator Database Administrator
http://xkcd.com/325
1
Now with more Madness!!
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
Perl Based Web Front End Servers Log Via Syslog Central Syslog Server PostgreSQL Central Data Store Open Source NMS Tools Custom Data Correlators
19
20
21
22
23
24
25
26
27
28
29
https://github.com/reyjrar/svnutils
30
“OSSEC is a scalable, multi-platform, open source Host-based Intrusion Detection System (HIDS). It has a powerful correlation and analysis engine, integrating log analysis, file integrity checking, Windows registry monitoring, centralized policy enforcement, rootkit detection, real-time alerting and active response. It runs on most operating systems, including Linux, OpenBSD, FreeBSD, MacOS, Solaris and Windows.”
31
brad.lhotsky@gmail.com https://twitter.com/reyjrar https://github.com/reyjrar
32