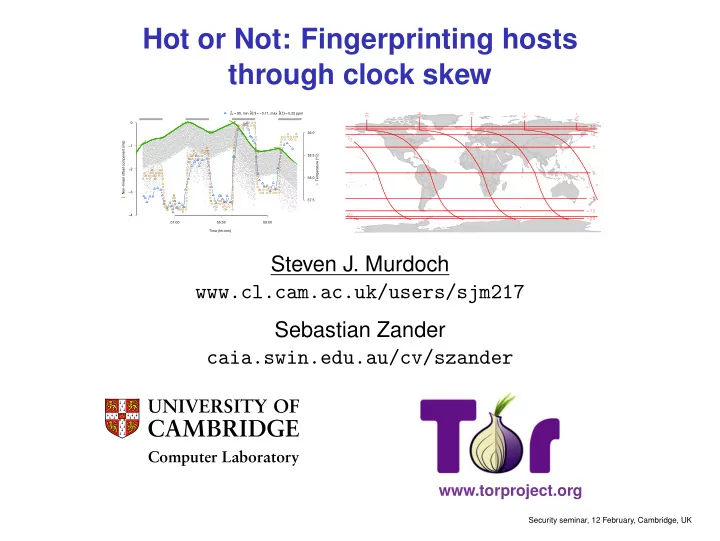
Hot or Not: Fingerprinting hosts through clock skew
Time (hh:mm) 01:00 05:00 09:00 Non−linear offset component (ms)
−
−4 −3 −2 −1 s ^c = 95, min s ^(t) = −0.11, max s ^(t) = 0.22 ppm
- ●
- ●
- ●
- ●
- ●
- 37.5
38.0 38.5 39.0 Temperature (°C)
- Steven J. Murdoch
www.cl.cam.ac.uk/users/sjm217 Sebastian Zander caia.swin.edu.au/cv/szander
Computer Laboratory www.torproject.org
Security seminar, 12 February, Cambridge, UK