SLIDE 1
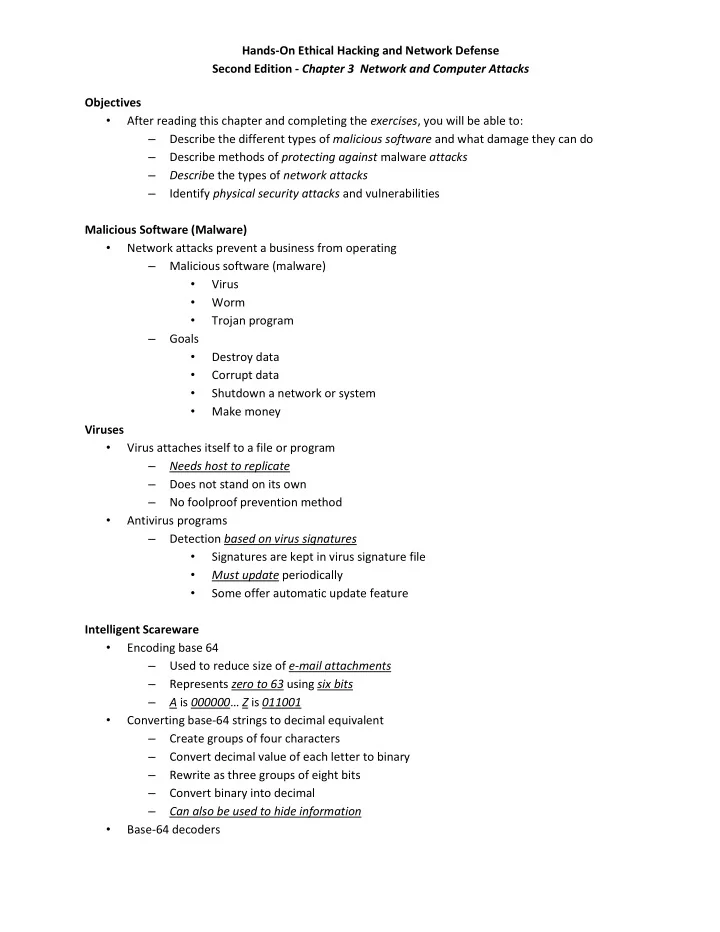
Hands-On Ethical Hacking and Network Defense Second Edition - Chapter 3 Network and Computer Attacks Objectives
- After reading this chapter and completing the exercises, you will be able to:
– Describe the different types of malicious software and what damage they can do – Describe methods of protecting against malware attacks – Describe the types of network attacks – Identify physical security attacks and vulnerabilities Malicious Software (Malware)
- Network attacks prevent a business from operating
– Malicious software (malware)
- Virus
- Worm
- Trojan program
– Goals
- Destroy data
- Corrupt data
- Shutdown a network or system
- Make money
Viruses
- Virus attaches itself to a file or program
– Needs host to replicate – Does not stand on its own – No foolproof prevention method
- Antivirus programs
– Detection based on virus signatures
- Signatures are kept in virus signature file
- Must update periodically
- Some offer automatic update feature
Intelligent Scareware
- Encoding base 64
– Used to reduce size of e-mail attachments – Represents zero to 63 using six bits – A is 000000… Z is 011001
- Converting base-64 strings to decimal equivalent
– Create groups of four characters – Convert decimal value of each letter to binary – Rewrite as three groups of eight bits – Convert binary into decimal – Can also be used to hide information
- Base-64 decoders