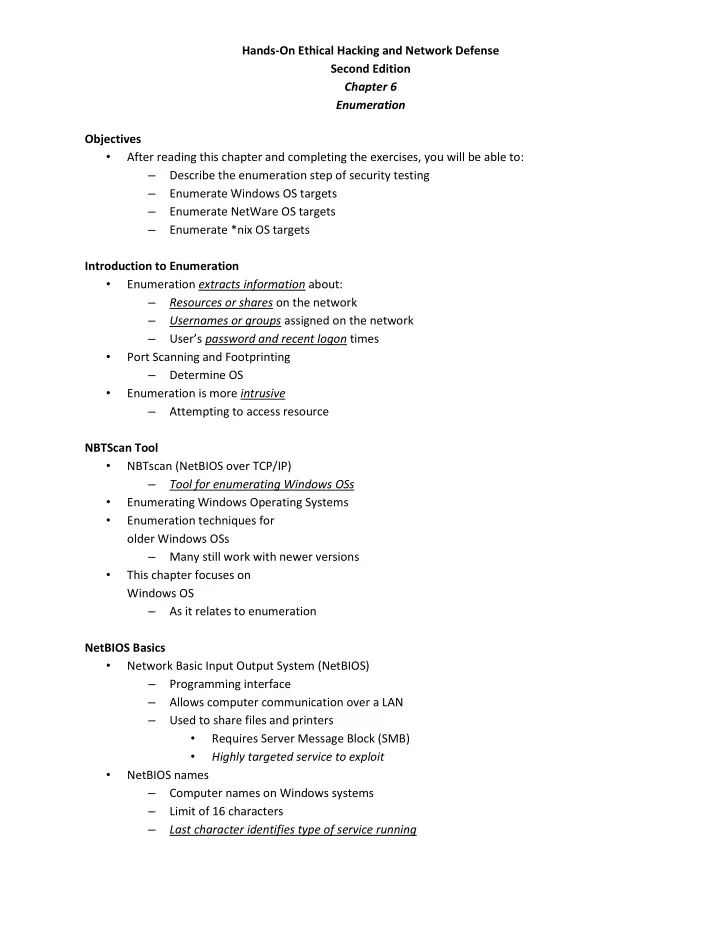
SLIDE 1
Hands-On Ethical Hacking and Network Defense Second Edition Chapter 6 Enumeration Objectives
- After reading this chapter and completing the exercises, you will be able to:
– Describe the enumeration step of security testing – Enumerate Windows OS targets – Enumerate NetWare OS targets – Enumerate *nix OS targets Introduction to Enumeration
- Enumeration extracts information about:
– Resources or shares on the network – Usernames or groups assigned on the network – User’s password and recent logon times
- Port Scanning and Footprinting
– Determine OS
- Enumeration is more intrusive
– Attempting to access resource NBTScan Tool
- NBTscan (NetBIOS over TCP/IP)
– Tool for enumerating Windows OSs
- Enumerating Windows Operating Systems
- Enumeration techniques for
- lder Windows OSs
– Many still work with newer versions
- This chapter focuses on
Windows OS – As it relates to enumeration NetBIOS Basics
- Network Basic Input Output System (NetBIOS)
– Programming interface – Allows computer communication over a LAN – Used to share files and printers
- Requires Server Message Block (SMB)
- Highly targeted service to exploit
- NetBIOS names