SLIDE 1
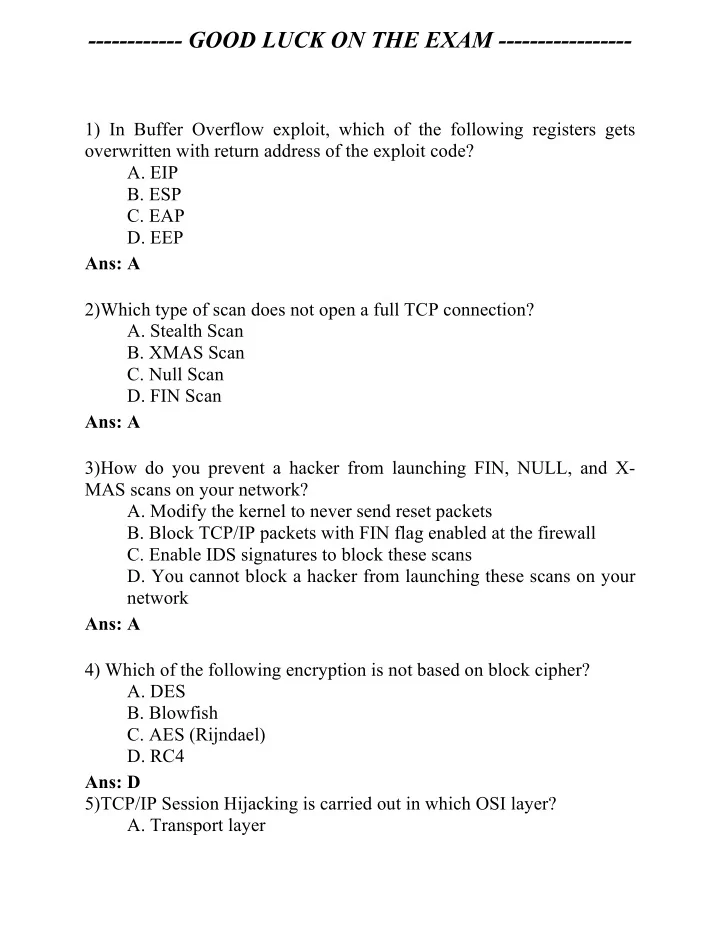
- ----------- GOOD LUCK ON THE EXAM -----------------
1) In Buffer Overflow exploit, which of the following registers gets
- verwritten with return address of the exploit code?
- A. EIP
- B. ESP
- C. EAP
- D. EEP
Ans: A 2)Which type of scan does not open a full TCP connection?
- A. Stealth Scan
- B. XMAS Scan
- C. Null Scan
- D. FIN Scan
Ans: A 3)How do you prevent a hacker from launching FIN, NULL, and X- MAS scans on your network?
- A. Modify the kernel to never send reset packets
- B. Block TCP/IP packets with FIN flag enabled at the firewall
- C. Enable IDS signatures to block these scans
- D. You cannot block a hacker from launching these scans on your
network Ans: A 4) Which of the following encryption is not based on block cipher?
- A. DES
- B. Blowfish
- C. AES (Rijndael)
- D. RC4
Ans: D 5)TCP/IP Session Hijacking is carried out in which OSI layer?
- A. Transport layer