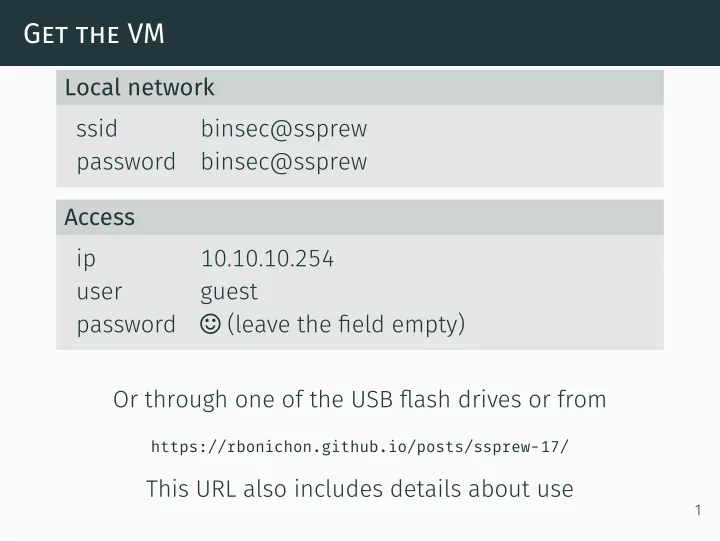
Get the VM
Local network ssid binsec@ssprew password binsec@ssprew Access ip 10.10.10.254 user guest password ⌣ (leave the field empty) Or through one of the USB flash drives or from
https://rbonichon.github.io/posts/ssprew-17/
This URL also includes details about use
1