SLIDE 1
Exercises, II part
Exercises, II part
Exercises, II part
Exercises, II part Forward Chaining: 12 Jul 2012 Exercises, II - - PDF document
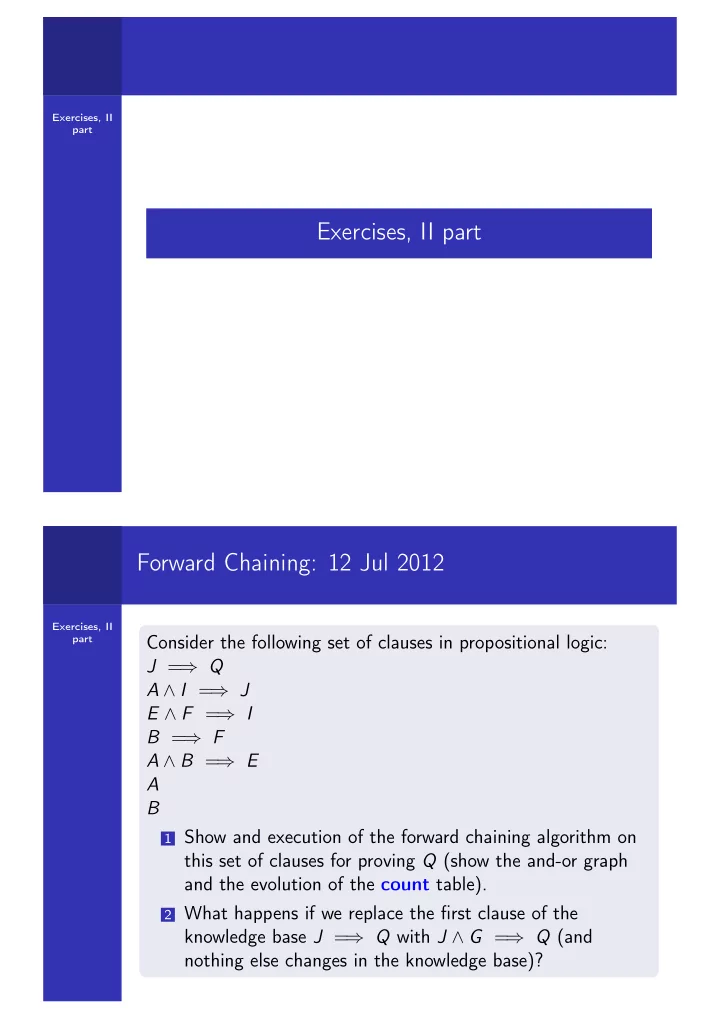
Exercises, II part Exercises, II part Forward Chaining: 12 Jul 2012 Exercises, II part Consider the following set of clauses in propositional logic: J = Q A I = J E F = I B = F A B = E A B 1 Show and execution
Exercises, II part
Exercises, II part
Exercises, II part
Exercises, II part
Exercises, II part
Exercises, II part
Exercises, II part
Exercises, II part
Exercises, II part
Exercises, II part
Exercises, II part