RFIDsec 2015 Security of Bistable Ring PUF
Example
10
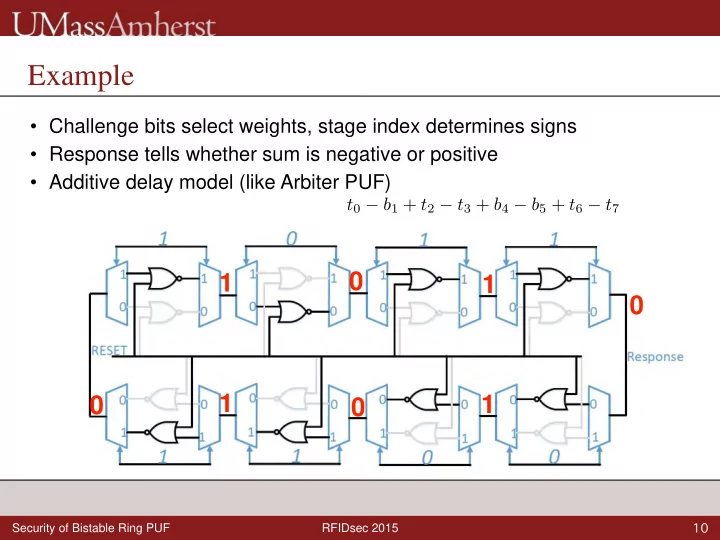
- Challenge bits select weights, stage index determines signs
- Response tells whether sum is negative or positive
- Additive delay model (like Arbiter PUF)
Example Challenge bits select weights, stage index determines signs - - PowerPoint PPT Presentation
Example Challenge bits select weights, stage index determines signs Response tells whether sum is negative or positive Additive delay model (like Arbiter PUF) t 0 b 1 + t 2 t 3 + b 4 b 5 + t 6 t 7 0 1 1 0 1 1 0
RFIDsec 2015 Security of Bistable Ring PUF
10
RFIDsec 2015 Security of Bistable Ring PUF
10
RFIDsec 2015 Security of Bistable Ring PUF
10
i=0..n−1
RFIDsec 2015 Security of Bistable Ring PUF
11
RFIDsec 2015 Security of Bistable Ring PUF
12
RFIDsec 2015 Security of Bistable Ring PUF
13
(6) D. Schuster, et al. Trust and Trustworthy Computing 2014
RFIDsec 2015 Security of Bistable Ring PUF
13
(6) D. Schuster, et al. Trust and Trustworthy Computing 2014
RFIDsec 2015 Security of Bistable Ring PUF
13
(6) D. Schuster, et al. Trust and Trustworthy Computing 2014
RFIDsec 2015 Security of Bistable Ring PUF
13
(6) D. Schuster, et al. Trust and Trustworthy Computing 2014
i=0..n−1
RFIDsec 2015 Security of Bistable Ring PUF
14
RFIDsec 2015 Security of Bistable Ring PUF
14
RFIDsec 2015 Security of Bistable Ring PUF
15
RFIDsec 2015 Security of Bistable Ring PUF
16
RFIDsec 2015 Security of Bistable Ring PUF
17
(1) U. Rühmair, et al, CCS, 2010.
RFIDsec 2015 Security of Bistable Ring PUF
18
RFIDsec 2015 Security of Bistable Ring PUF
19
Sun Electronics EC12 Environmental Chamber
RFIDsec 2015 Security of Bistable Ring PUF
20
(1) Schuster et al. TRUST 2014