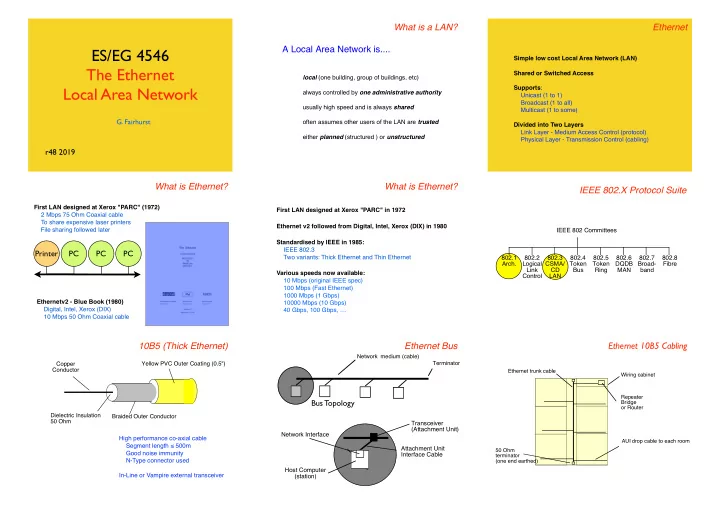
ES/EG 4546 The Ethernet Local Area Network
- G. Fairhurst
r48 2019
What is a LAN?
local (one building, group of buildings, etc) always controlled by one administrative authority usually high speed and is always shared
- ften assumes other users of the LAN are trusted
either planned (structured ) or unstructured
A Local Area Network is.... Ethernet
Simple low cost Local Area Network (LAN) Shared or Switched Access Supports: Unicast (1 to 1) Broadcast (1 to all) Multicast (1 to some) Divided into Two Layers Link Layer - Medium Access Control (protocol) Physical Layer - Transmission Control (cabling)
What is Ethernet?
First LAN designed at Xerox "PARC" (1972) 2 Mbps 75 Ohm Coaxial cable To share expensive laser printers File sharing followed later Ethernetv2 - Blue Book (1980) Digital, Intel, Xerox (DIX) 10 Mbps 50 Ohm Coaxial cable
Printer PC PC PC
What is Ethernet?
Standardised by IEEE in 1985: IEEE 802.3 Two variants: Thick Ethernet and Thin Ethernet Various speeds now available: 10 Mbps (original IEEE spec) 100 Mbps (Fast Ethernet) 1000 Mbps (1 Gbps) 10000 Mbps (10 Gbps) 40 Gbps, 100 Gbps, … First LAN designed at Xerox "PARC" in 1972 Ethernet v2 followed from Digital, Intel, Xerox (DIX) in 1980
IEEE 802.X Protocol Suite
IEEE 802 Committees 802.1 Arch. 802.3 CSMA/ CD LAN 802.4 Token Bus 802.5 Token Ring 802.6 DQDB MAN 802.2 Logical Link Control 802.7 Broad- band 802.8 Fibre
10B5 (Thick Ethernet)
!Yellow PVC Outer Coating (0.5") Dielectric Insulation 50 Ohm Copper Conductor Braided Outer Conductor High performance co-axial cable Segment length ≤ 500m Good noise immunity N-Type connector used In-Line or Vampire external transceiver
Ethernet Bus
Bus Topology
Network medium (cable) Terminator
Host Computer (station) Network Interface Transceiver (Attachment Unit) Attachment Unit Interface Cable
Ethernet 10B5 Cabling
Ethernet trunk cable AUI drop cable to each room 50 Ohm terminator (one end earthed) Wiring cabinet Repeater Bridge
- r Router