1 CSE 123 Computer Networks
Lecture 3: Data Link I – Framing and Error Control July 10, 2006
Chris Kanich
Portions courtesy Jeannie Albrecht, Robin Kravets and Steve Lumetta
CSE 123 Lecture 3 – Framing and Error Control
Last time: Physical link layer
Tasks
Encode binary data from source node into signals
that physical links carry
Signal is decoded back into binary data at receiving
node
Work performed by network adapter at sender and
receiver
Synchronous encoding algorithms
NRZ, NRZI, Manchester, 4B/5B
CSE 123 Lecture 3 – Framing and Error Control CSE 123 Lecture 3 – Framing and Error Control
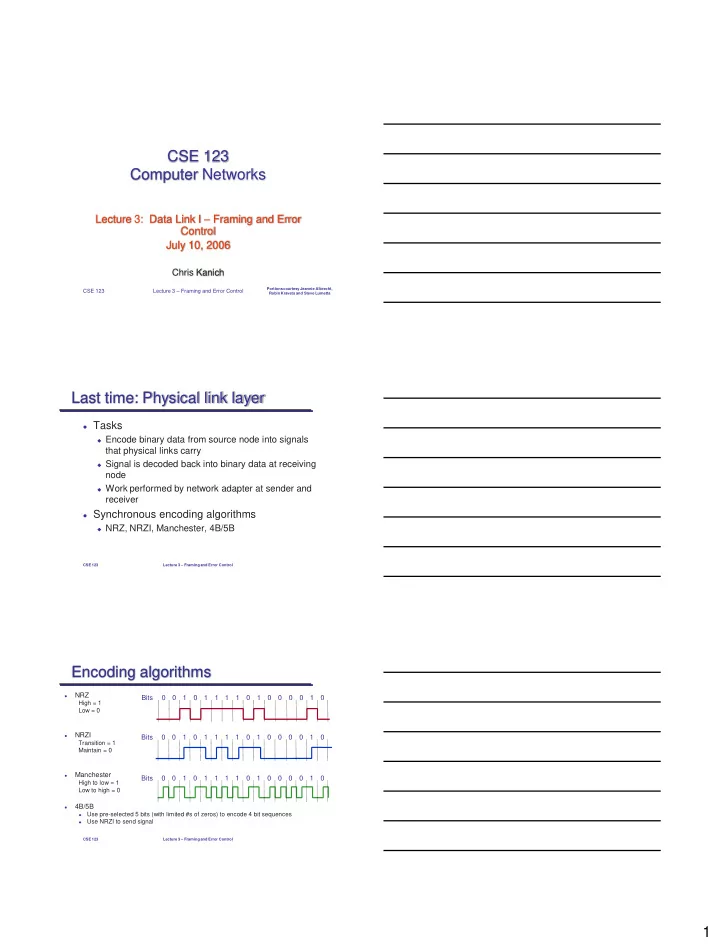
Encoding algorithms
NRZ
High = 1 Low = 0
NRZI
Transition = 1 Maintain = 0
Manchester
High to low = 1 Low to high = 0
4B/5B
Use pre-selected 5 bits (with limited #s of zeros) to encode 4 bit sequences
Use NRZI to send signal
Bits 1 1 1 1 1 1 1 Bits 1 1 1 1 1 1 1 Bits 1 1 1 1 1 1 1