SLIDE 1
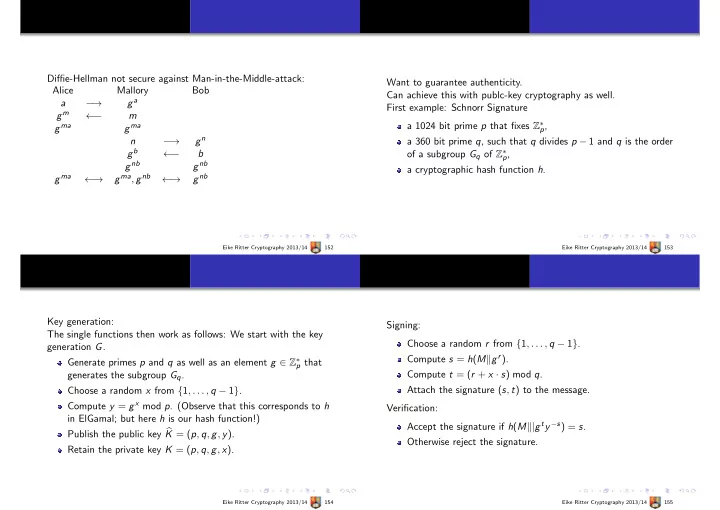
Diffie-Hellman not secure against Man-in-the-Middle-attack: Alice Mallory Bob a − → ga gm ← − m gma gma n − → gn gb ← − b gnb gnb gma ← → gma, gnb ← → gnb
Eike Ritter Cryptography 2013/14 152
Want to guarantee authenticity. Can achieve this with publc-key cryptography as well. First example: Schnorr Signature a 1024 bit prime p that fixes Z∗
p,
a 360 bit prime q, such that q divides p − 1 and q is the order
- f a subgroup Gq of Z∗
p,
a cryptographic hash function h.
Eike Ritter Cryptography 2013/14 153
Key generation: The single functions then work as follows: We start with the key generation G. Generate primes p and q as well as an element g ∈ Z∗
p that
generates the subgroup Gq. Choose a random x from {1, . . . , q − 1}. Compute y = gx mod p. (Observe that this corresponds to h in ElGamal; but here h is our hash function!) Publish the public key K = (p, q, g, y). Retain the private key K = (p, q, g, x).
Eike Ritter Cryptography 2013/14 154
Signing: Choose a random r from {1, . . . , q − 1}. Compute s = h(Mgr). Compute t = (r + x · s) mod q. Attach the signature (s, t) to the message. Verification: Accept the signature if h(M|gty−s) = s. Otherwise reject the signature.
Eike Ritter Cryptography 2013/14 155