Cybercrime
Part II Tyler Moore
Computer Science & Engineering Department, SMU, Dallas, TX
October 25, 2012
Outline
2 / 28
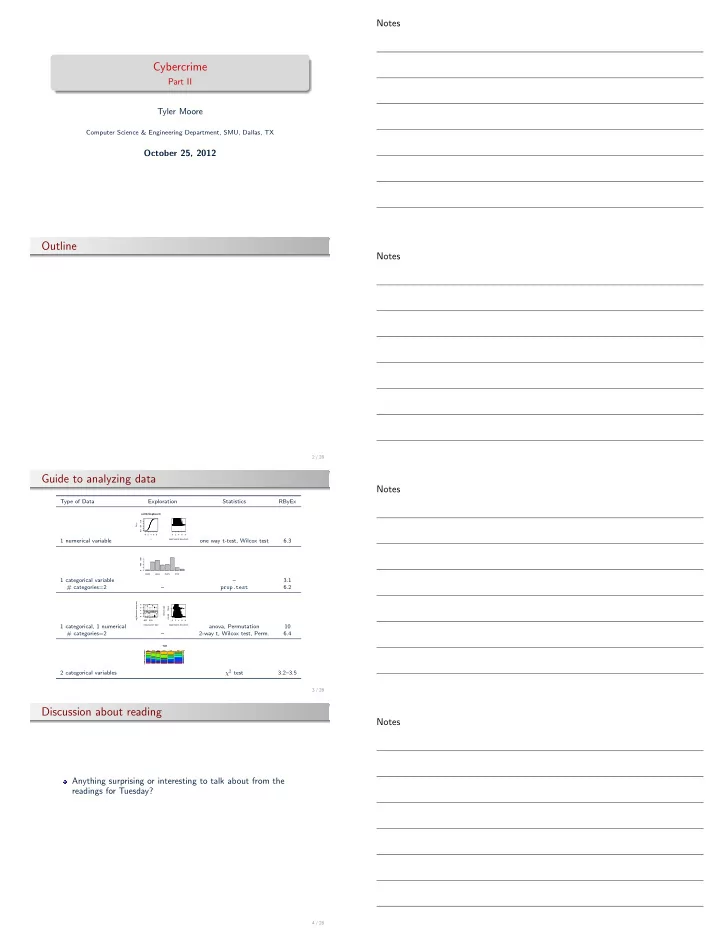
Guide to analyzing data
Type of Data Exploration Statistics RByEx 1 numerical variable
2 4 6 8 0.0 0.4 0.8 ecdf(br$logbreach) x Fn(x) 2 4 6 8 log(#records breached)
- ne way t-test, Wilcox test
6.3 1 categorical variable
CARD HACK PHYS STAT 400 800
– 3.1 # categories=2 – prop.test 6.2 1 categorical, 1 numerical
- BSF
EDU 2 4 6 8 Organization Type log(#records breached) 2 4 6 8 FALSE TRUE log(#records breached) Breach type
- ●
- anova, Permutation
10 # categories=2 – 2-way t, Wilcox test, Perm. 6.4 2 categorical variables
TOH
BSF BSO BSR EDU GOV MED NGO CARD DISC HACK INSD PHYS PORT STAT UNKN
χ2 test 3.2–3.5
3 / 28
Discussion about reading
Anything surprising or interesting to talk about from the readings for Tuesday?
4 / 28