Cloudare Provider
The Cloudare provider is used to interact with resources supported by Cloudare. The provider needs to be congured with the proper credentials before it can be used. Use the navigation to the left to read about the available resources.
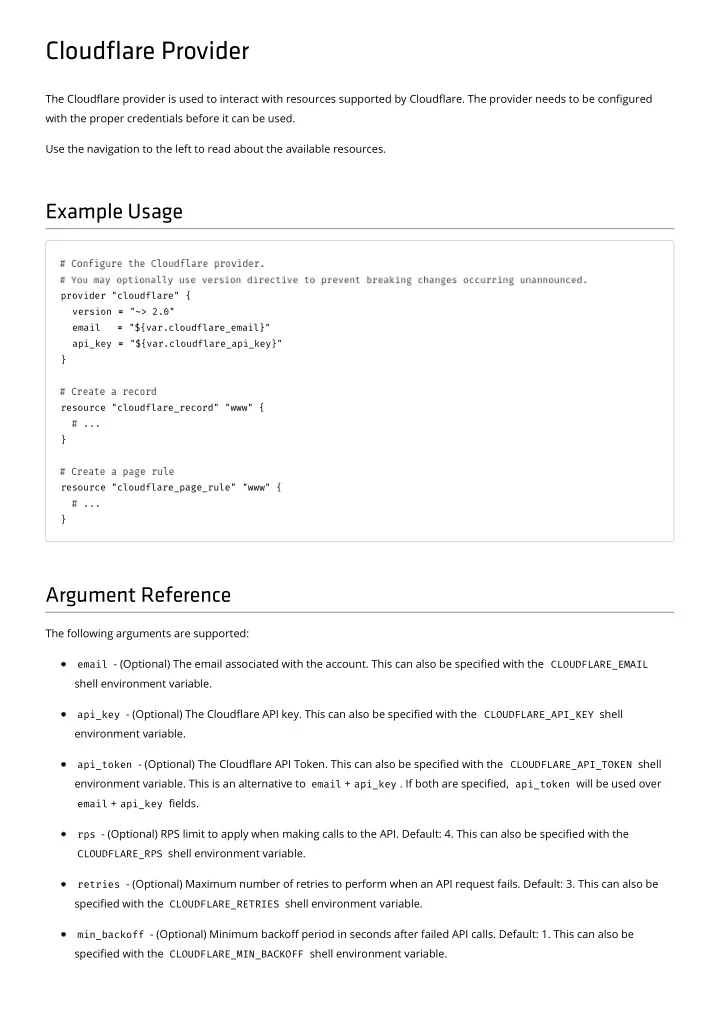
Example Usage
provider "cloudflare" { version = = "~> 2.0" email = = "${var.cloudflare_email}" api_key = = "${var.cloudflare_api_key}" } resource "cloudflare_record" "www" { } resource "cloudflare_page_rule" "www" { }
Argument Reference
The following arguments are supported:
email - (Optional) The email associated with the account. This can also be specied with the CLOUDFLARE_EMAIL
shell environment variable.
api_key - (Optional) The Cloudare API key. This can also be specied with the CLOUDFLARE_API_KEY shell
environment variable.
api_token - (Optional) The Cloudare API Token. This can also be specied with the CLOUDFLARE_API_TOKEN shell
environment variable. This is an alternative to email + api_key . If both are specied, api_token will be used over
email + api_key elds. rps - (Optional) RPS limit to apply when making calls to the API. Default: 4. This can also be specied with the CLOUDFLARE_RPS shell environment variable. retries - (Optional) Maximum number of retries to perform when an API request fails. Default: 3. This can also be
specied with the CLOUDFLARE_RETRIES shell environment variable.
min_backoff - (Optional) Minimum backo period in seconds after failed API calls. Default: 1. This can also be
specied with the CLOUDFLARE_MIN_BACKOFF shell environment variable.