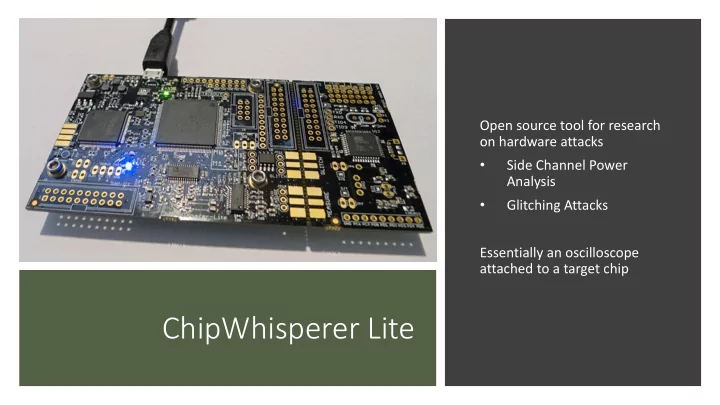
ChipWhisperer Lite
Open source tool for research
- n hardware attacks
- Side Channel Power
Analysis
- Glitching Attacks
Essentially an oscilloscope attached to a target chip
ChipWhisperer Lite Modeling Power Consumption Every device requires - - PowerPoint PPT Presentation
Open source tool for research on hardware attacks Side Channel Power Analysis Glitching Attacks Essentially an oscilloscope attached to a target chip ChipWhisperer Lite Modeling Power Consumption Every device requires power to run
Open source tool for research
Analysis
Essentially an oscilloscope attached to a target chip
Every device requires power to run (static power) Data moving through the device changes power consumption (dynamic power) Dynamic Power – Current required to charge or discharge data lines
00110000 transitioning to 00100011
Force target device to encrypt many different things Log traces of these different encryptions Analyze these different traces and determine subkeys BREAK ENCRYPTION!
Setting up target device
Setting up oscilloscope
Analyze Traces
Results table: first row (in white) is the “result key” from analysis. Note this is the same key as used to generate the traces!
data
and known
Above equation is the relationship between a hypothetical guess for each XOR equation (both key and data to encrypt) compared to the actual change in the trace
Apply hypothetical guesses