1
channel and fault attacks Jasper van Woudenberg @jzvw January 10, - - PowerPoint PPT Presentation
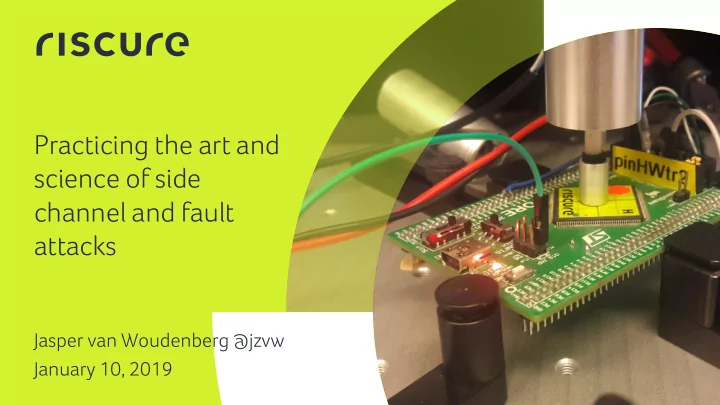
channel and fault attacks Jasper van Woudenberg @jzvw January 10, - - PowerPoint PPT Presentation
Practicing the art and science of side channel and fault attacks Jasper van Woudenberg @jzvw January 10, 2019 1 Our vision certificate recommendations countermeasures 2 Where we are today Science Art Bit of both certificate 2 weeks
2
Our vision
recommendations certificate countermeasures
3
Bit of both Science Art
Where we are today
recommendations certificate countermeasures DPA, TVLA DFA, FI success% Signal processing Leakage id/model Tuning FI setup
2 weeks – 2 months (single algorithm)
4
Power side channel analysis and fault injection
5
Bit of both Science
Where we are today
recommendations certificate countermeasures DPA, TVLA DFA, FI success%
Art
Signal processing Leakage id/model Tuning FI setup
6
7
Power Analysis
Leakage modeling Signal processing
8
Signal processing
Raw trace Processed trace
9
Misalignment
10
Points of interest selection
Data leakage Noise Samples showing statis istic ical al dependenc ndency between intermediate (key-related) data and power consumption.
11
EM leakage location finding
Some delivers truth but too costly Some cheaper but misleading
Pics origin: “EM-scanning” by Albert Spruyt
Key rank (5M) Ghost peak dist.(8M) Intermediates corr. (3M) Spectral intensity (1) Input corr. (1M) Output corr. (1M)
12
Open research questions
- How to find good EM spots
without doing T-testing on each spot
- How to automate the combined
problem of filtering, alignment, etc?
13
Fault injection
14
FI output
15
Open research questions
- What exactly happens to a circuit
when faulted, to inform countermeasures
- More software scalable FI attacks,
a la CLKscrew
16
Bit of both Science
Where we are today
recommendations certificate countermeasures DPA, TVLA DFA, FI success%
Art
Signal processing Leakage id/model Tuning FI setup
17
t: µB: µA:
Sboxes, R5
TVLA (T-testing)
MixColumns, R5
18
Open research questions
- How exploitable are T-spikes in
practice?
19
DPA key recovery
Number of traces Key Byte Rank AES key bytes 0-15
20
Open research questions
- So far, it’s hard to beat CPA in
terms of time efficiency. New attacks are interesting if they significantly reduce attack time from acquisition to key extraction, apply to all targets, and are unsupervised (and complete start to finish in the
- rder of weeks)
21
Voltage (V) Length (ns)
Glitch length vs. glitch voltage (XMEGA)
22
Open research questions
- We rarely perform Differential
Fault Analysis. If we can exploit JTAG or Boot, we get more. How to harden those?
23
Bit of both Science
Where we are today
recommendations certificate countermeasures DPA, TVLA DFA, FI success%
Art
Signal processing Leakage id/model Tuning FI setup
24
Certify
- Goal is to have objective pass/fail criteria
- Common Criteria / EMVco / GP TEE:
- Expertise, equipment used, time elapsed, samples used,
information available, open samples
- (#traces not directly relevant, nor FI success %!)
- As objective as we know how to make it
25
Open research questions
- What is an objective measure that
represents device security?
26
Improve
- We can deduce some information:
- Timing of leakage / fault
- Amount of leakage / fault success rate
- Type of leakage
- Turning this into countermeasures is nontrivial
- Whack-a-mole happens
27
Open research questions
- How to automatically create
countermeasures based on test results?
- Results on FPGA/non-secure
microcontroller do not translate to secure microcontrollers or
- SoCs. More results on the latter
categories are needed.
28
Current research: Deep learning for SCA
29
Before
Leakage modeling Signal processing
30
After
Metrics Leakage info
31
Breaking AES with First-Order Masking
- Target published in 2013 (http://www.dpacontest.org/v4/)
- 40k traces available
- AES-256 (Atmel ATMega-163 smart card)
- Countermeasure: Rotating S-box Masking (RSM)
32
How does DPA contest V4 masking work?
- Masking is expensive in performance and memory
- Rotating mask helps by pre-computing masked S-boxes
33
Breaking AES with First-Order Masking
Neural Network: Input Layer > ConvLayer > 50 > 50 > 50 > Output Layer Training/validation/test sets: 36000/2000/2000 traces Leakage Model: HW of S-Box Out (Round 1) → 9 classes
1/9
Results for key byte 0:
The processing of 8 traces is sufficient to recover the key
34
Open research questions
- We rarely perform 2nd order
attacks, because sample combing is infeasible due to noise and limited time. How to find those samples efficiently?
35
Our visualization method
Conv. Conv. Pooling Pooling Input Data Feature Map Dense Layers Output Feature Combination + Classification Feature Extraction + Dimensionality Reduction
HW = 5
36
Results (unprotected target)
Raw trace T-test (first round key byte) Our visualization method
CPA succeeds CPA fails
37
DL conclusions so far
- DL can exploit and identify leakage
- DL does SCA art + science and scales
- Hardware crypto still presents challenges
- DL still requires humans in tuning a network
38
Active research areas
- Machine learning for SCA
- FI outside of lab conditions /
larger distance
- Design time analysis
- SCA on simulator
- FI on simulator
39
Wrapping up
40
Conclusion
- Automation is needed for the scale of the issues
- Many interesting research questions lay on this path
- We are looking to collaborate on such topics
recommendations certificate countermeasures
41
Challenge your security
Riscur cure B.V. Frontier Building, Delftechpark 49 2628 XJ Delft The Netherlands Phone: +31 15 251 40 90 www.riscure.com Riscur cure North America ica 550 Kearny St., Suite 330 San Francisco, CA 94108 USA Phone: +1 650 646 99 79 inforequest@riscure.com Riscur cure Chin ina Room 2030-31, No. 989, Changle Road, Shanghai 200031 China Phone: +86 21 5117 5435 inforcn@riscure.com