1
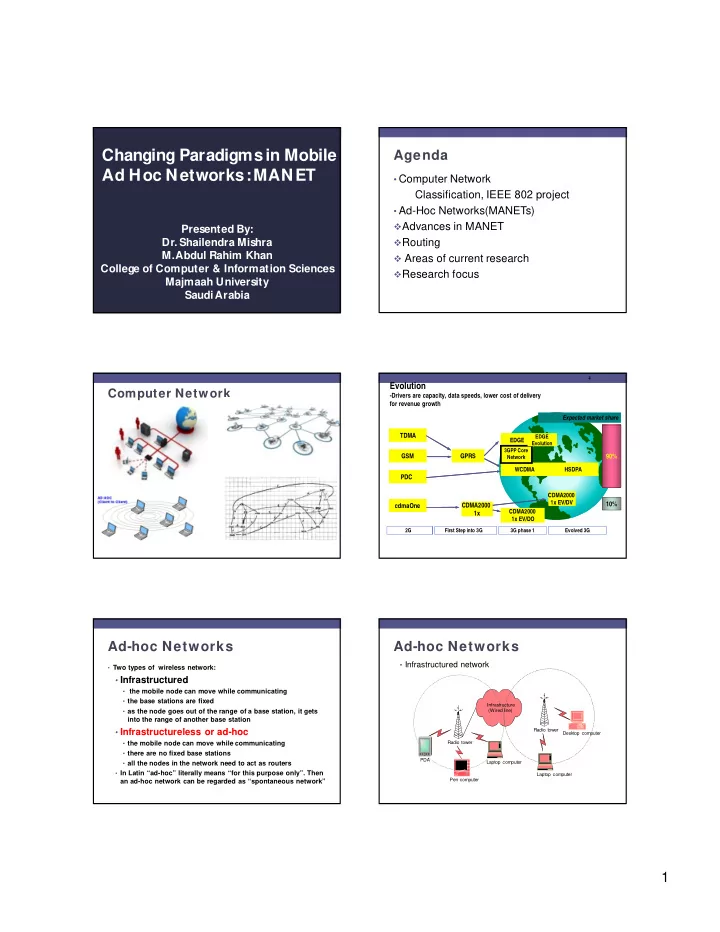
Changing Paradigms in Mobile Ad Hoc Networks : MANET
Presented By:
- Dr. Shailendra Mishra
- M. Abdul Rahim Khan
College of Computer & Information Sciences Majmaah University Saudi Arabia
Agenda
- Computer Network
Classification, IEEE 802 project
- Ad-Hoc Networks(MANETs)
Advances in MANET Routing Areas of current research Research focus
Computer Network
4
cdmaOne cdmaOne GSM GSM TDMA TDMA
2G
PDC PDC CDMA2000 1x CDMA2000 1x
First Step into 3G
GPRS GPRS 90% 10%
Evolution
- Drivers are capacity, data speeds, lower cost of delivery
for revenue growth EDGE EDGE WCDMA WCDMA CDMA2000 1x EV/DV CDMA2000 1x EV/DV
3G phase 1 Evolved 3G 3GPP Core Network CDMA2000 1x EV/DO CDMA2000 1x EV/DO HSDPA HSDPA Expected market share EDGE Evolution EDGE Evolution
Ad-hoc Networks
- Two types of wireless network:
- Infrastructured
- the mobile node can move while communicating
- the base stations are fixed
- as the node goes out of the range of a base station, it gets
into the range of another base station
- Infrastructureless or ad-hoc
- the mobile node can move while communicating
- there are no fixed base stations
- all the nodes in the network need to act as routers
- In Latin “ad-hoc” literally means “for this purpose only”. Then
an ad-hoc network can be regarded as “spontaneous network”
Ad-hoc Networks
- Infrastructured network
PDA Pen computer Radio tower Laptop computer Radio tower Infrastructure (Wired line) Desktop computer Laptop computer