Chenyang Lu CSE 467S 1
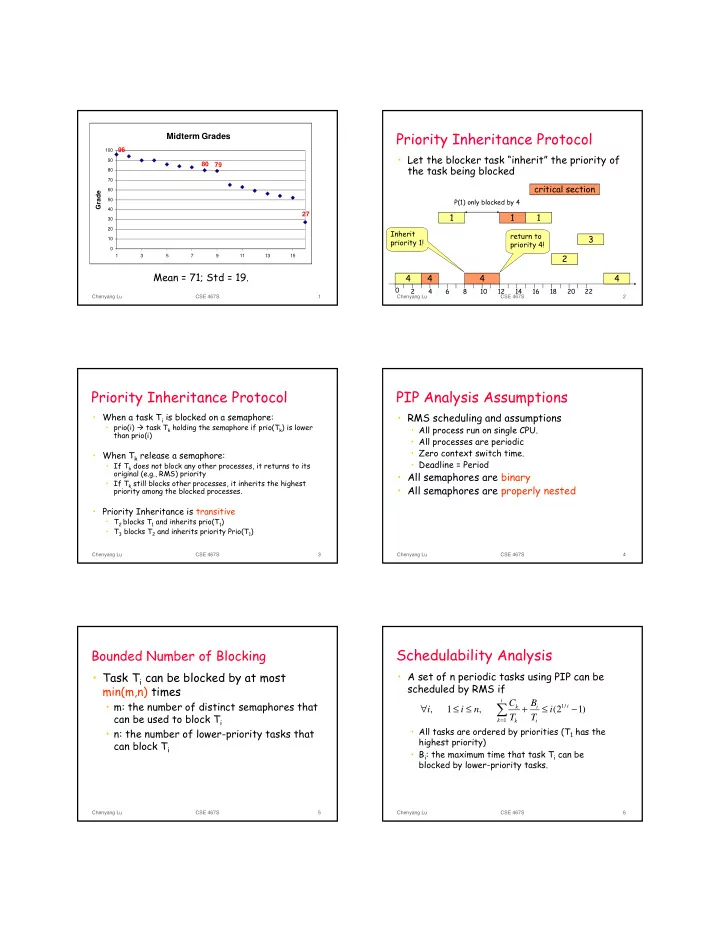
Midterm Grades
79 80 27 96
10 20 30 40 50 60 70 80 90 100 1 3 5 7 9 11 13 15
Grade
Mean = 71; Std = 19.
Chenyang Lu CSE 467S 2
Priority Inheritance Protocol
- Let the blocker task “inherit” the priority of
the task being blocked
1 4 4 4
2 4 6 8 10 12 14 16 18 20 22
1 1 critical section
P(1) only blocked by 4
Inherit priority 1!
2 3 4
return to priority 4!
Chenyang Lu CSE 467S 3
Priority Inheritance Protocol
- When a task Ti is blocked on a semaphore:
- prio(i) task Tk holding the semaphore if prio(Tk) is lower
than prio(i)
- When Tk release a semaphore:
- If Tk does not block any other processes, it returns to its
- riginal (e.g., RMS) priority
- If Tk still blocks other processes, it inherits the highest
priority among the blocked processes.
- Priority Inheritance is transitive
- T2 blocks T1 and inherits prio(T1)
- T3 blocks T2 and inherits priority Prio(T1)
Chenyang Lu CSE 467S 4
PIP Analysis Assumptions
- RMS scheduling and assumptions
- All process run on single CPU.
- All processes are periodic
- Zero context switch time.
- Deadline = Period
- All semaphores are binary
- All semaphores are properly nested
Chenyang Lu CSE 467S 5
Bounded Number of Blocking
- Task Ti can be blocked by at most
min(m,n) times
- m: the number of distinct semaphores that
can be used to block Ti
- n: the number of lower-priority tasks that
can block Ti
Chenyang Lu CSE 467S 6
Schedulability Analysis
- A set of n periodic tasks using PIP can be
scheduled by RMS if
- All tasks are ordered by priorities (T1 has the
highest priority)
- Bi: the maximum time that task Ti can be
blocked by lower-priority tasks.
∑
=
− ≤ + ≤ ≤ ∀
i k i i i k k
i T B T C n i i
1 / 1