ECB CBC CTR Cryptomeria cipher Security for Block ciper modes
Clarification about attacker power
In security games, attacker can only do efficient operations Importantly: attacker cannot search through all bitstrings, as the number of possible bistrings increases exponentially with the length Formally: attacker is probabibilistic polynomial Turing machine
Eike Ritter Cryptography 2013/14 60 ECB CBC CTR Cryptomeria cipher Security for Block ciper modes
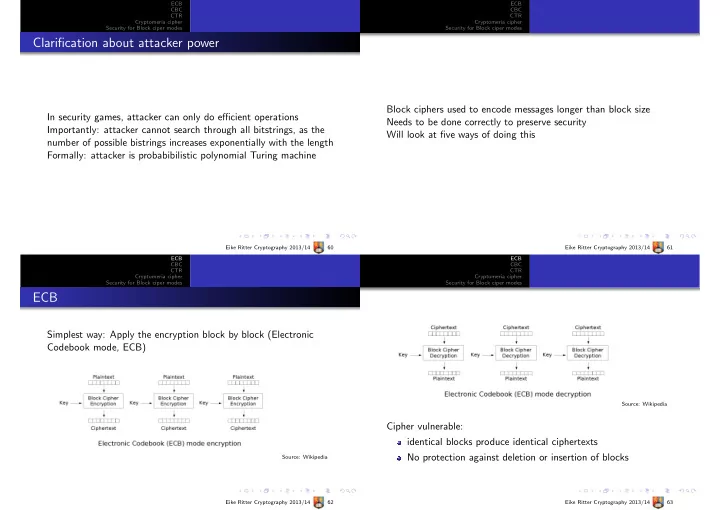
Block ciphers used to encode messages longer than block size Needs to be done correctly to preserve security Will look at five ways of doing this
Eike Ritter Cryptography 2013/14 61 ECB CBC CTR Cryptomeria cipher Security for Block ciper modes
ECB
Simplest way: Apply the encryption block by block (Electronic Codebook mode, ECB)
Source: Wikipedia Eike Ritter Cryptography 2013/14 62 ECB CBC CTR Cryptomeria cipher Security for Block ciper modes Source: Wikipedia
Cipher vulnerable: identical blocks produce identical ciphertexts No protection against deletion or insertion of blocks
Eike Ritter Cryptography 2013/14 63