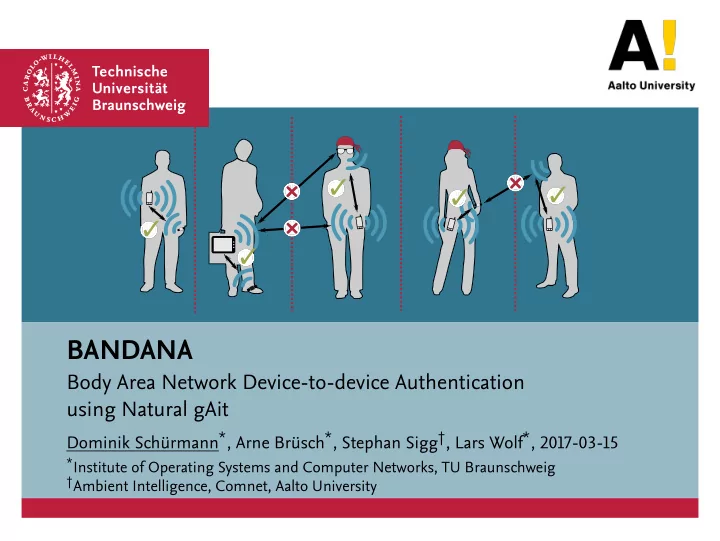
BANDANA
Body Area Network Device-to-device Authentication using Natural gAit
Dominik Schürmann*, Arne Brüsch*, Stephan Sigg†, Lars Wolf*, 2017-03-15
*Institute of Operating Systems and Computer Networks, TU Braunschweig †Ambient Intelligence, Comnet, Aalto University