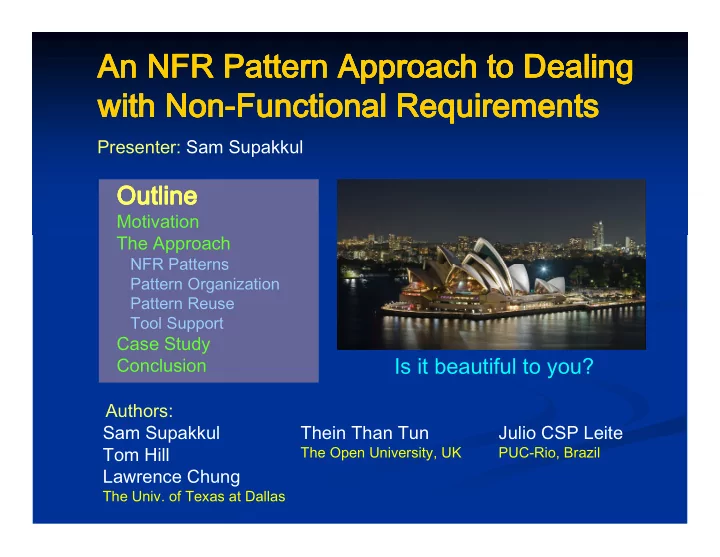
An NFR Pattern Approach to Dealing An NFR Pattern Approach to Dealing An NFR Pattern Approach to Dealing An NFR Pattern Approach to Dealing with Non with Non with Non with Non-
- Functional Requirements
Functional Requirements Functional Requirements Functional Requirements
Sam Supakkul Tom Hill Lawrence Chung
The Univ. of Texas at Dallas
Julio CSP Leite
PUC-Rio, Brazil
Thein Than Tun
The Open University, UK
Presenter: Sam Supakkul
Outline Outline Outline Outline
Motivation The Approach
NFR Patterns Pattern Organization Pattern Reuse Tool Support