An Evil Copy: How the Loader Betrays You Xinyang Ge 1,3 , Mathias - PowerPoint PPT Presentation
An Evil Copy: How the Loader Betrays You Xinyang Ge 1,3 , Mathias Payer 2 and Trent Jaeger 3 Microsoft Research 1 Purdue University 2 Penn State University 3 Systems and Internet Infrastructure Security Laboratory (SIIS) Page 1 Problem: A
An Evil Copy: How the Loader Betrays You Xinyang Ge 1,3 , Mathias Payer 2 and Trent Jaeger 3 Microsoft Research 1 Purdue University 2 Penn State University 3 Systems and Internet Infrastructure Security Laboratory (SIIS) Page 1
Problem: A Motivating Example // test.c // main.c const int foo = 10; extern const int foo; int main() { *(int *)&foo = 100; return 0; } Systems and Internet Infrastructure Security Laboratory (SIIS) Page 2
Problem: A Motivating Example // test.c // main.c const int foo = 10; extern const int foo; int main() { *(int *)&foo = 100; return 0; } Systems and Internet Infrastructure Security Laboratory (SIIS) Page 2
Problem: A Motivating Example • 1 Executable ‣ cc main.c test.c • 1 Executable + 1 Library ‣ cc -fPIC –shared test.c –o libtest.so ‣ cc [–fPIE] main.c -L. –ltest Systems and Internet Infrastructure Security Laboratory (SIIS) Page 3
Problem: A Motivating Example • 1 Executable ‣ cc main.c test.c • 1 Executable + 1 Library ‣ cc -fPIC –shared test.c –o libtest.so ‣ cc [-fPIE] main.c -L. –ltest Systems and Internet Infrastructure Security Laboratory (SIIS) Page 3
Problem: A Motivating Example • 1 Executable ‣ cc main.c test.c • 1 Executable + 1 Library ‣ cc -fPIC –shared test.c –o libtest.so …Nothing happened? ‣ cc [-fPIE] main.c -L. –ltest Systems and Internet Infrastructure Security Laboratory (SIIS) Page 3
Problem: A Motivating Example • 1 Executable ‣ cc main.c test.c • 1 Executable + 1 Library ‣ cc -fPIC –shared test.c –o libtest.so …Nothing happened? ‣ cc [-fPIE] main.c -L. –ltest • 1 Executable + 1 Library ‣ cc -fPIC –shared test.c –o libtest.so ‣ cc –fPIC main.c -L. –ltest Systems and Internet Infrastructure Security Laboratory (SIIS) Page 3
Problem: A Motivating Example • 1 Executable ‣ cc main.c test.c • 1 Executable + 1 Library ‣ cc -fPIC –shared test.c –o libtest.so …Nothing happened? ‣ cc [-fPIE] main.c -L. –ltest • 1 Executable + 1 Library ‣ cc -fPIC –shared test.c –o libtest.so ‣ cc –fPIC main.c -L. –ltest Systems and Internet Infrastructure Security Laboratory (SIIS) Page 3
What happened so far... non-PIC executable PIC executable local “foo” foreign “foo” …Nothing happened? Obviously, foo is not in read-only memory in the above case, but WHY ? Systems and Internet Infrastructure Security Laboratory (SIIS) Page 4
Building Process compiling linking loading Systems and Internet Infrastructure Security Laboratory (SIIS) Page 5
Building Process compiling linking loading Systems and Internet Infrastructure Security Laboratory (SIIS) Page 5
What does “extern” mean // main.c extern const int foo; int main() { *(int *)&foo = 100; return 0; } Systems and Internet Infrastructure Security Laboratory (SIIS) Page 6
What does “extern” mean foo is defined in a different file but // main.c still in the same image ( w/o -fPIC flag ) extern const int foo; int main() { *(int *)&foo = 100; return 0; } foo is defined in a different file and potentially in a different image ( w/ -fPIC flag ) Systems and Internet Infrastructure Security Laboratory (SIIS) Page 6
What does “extern” mean foo is defined in a different file but // main.c still in the same image ( w/o -fPIC flag ) extern const int foo; int main() { *(int *)&foo = 100; return 0; } foo is defined in a different file and potentially in a different image ( w/ -fPIC flag ) Systems and Internet Infrastructure Security Laboratory (SIIS) Page 6
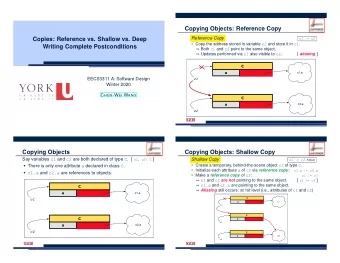
foo is defined in the same image // main.o – assuming same image <main>: push %rbp mov %rsp,%rbp mov $0x64,offset_to_foo(%rip) mov $0x0,%rax pop %rbp ret Systems and Internet Infrastructure Security Laboratory (SIIS) Page 7
foo is defined in the same image // main.o – assuming same image The compiler assumes <main>: foo’s location can be push %rbp statically determined by mov %rsp,%rbp the linker, and emits a mov $0x64,offset_to_foo(%rip) mov $0x0,%rax single MOV instruction to pop %rbp write to foo. ret Systems and Internet Infrastructure Security Laboratory (SIIS) Page 7
foo is defined in the same image data foo // main.o – assuming same image The compiler assumes <main>: foo’s location can be push %rbp statically determined by mov %rsp,%rbp GOT the linker, and emits a mov $0x64,offset_to_foo(%rip) mov $0x0,%rax single MOV instruction to pop %rbp write to foo. ret code Systems and Internet Infrastructure Security Laboratory (SIIS) Page 7
What does “extern” mean foo is defined in a different file but // main.c still in the same image ( w/o -fPIC flag ) extern const int foo; int main() { *(int *)&foo = 100; return 0; } foo is defined in a different file and potentially in a different image ( w/ -fPIC flag ) Systems and Internet Infrastructure Security Laboratory (SIIS) Page 8
foo is defined in a di ff erent image // main.o – assuming same image <main>: push %rbp mov %rsp,%rbp mov offset_to_foo_got(%rip),%rax mov $0x64,(%rax) mov $0x0,%rax pop %rbp ret Systems and Internet Infrastructure Security Laboratory (SIIS) Page 8
foo is defined in a di ff erent image The compiler assumes // main.o – assuming same image foo’s loca;on cannot be <main>: sta;cally determined push %rbp and emits two MOV mov %rsp,%rbp instruc;ons: one to mov offset_to_foo_got(%rip),%rax retrieve foo’s address mov $0x64,(%rax) mov $0x0,%rax from its GOT slot, and pop %rbp the other to actually ret write to foo. Systems and Internet Infrastructure Security Laboratory (SIIS) Page 8
foo is defined in a di ff erent image data The compiler assumes // main.o – assuming same image foo’s loca;on cannot be <main>: sta;cally determined push %rbp and emits two MOV mov %rsp,%rbp instruc;ons: one to GOT mov offset_to_foo_got(%rip),%rax retrieve foo’s address mov $0x64,(%rax) foo’s address mov $0x0,%rax from its GOT slot, and pop %rbp the other to write to code ret foo. Systems and Internet Infrastructure Security Laboratory (SIIS) Page 8
Without –fPIC flag, GCC and Clang on Linux assumes foo is defined in the same image. Systems and Internet Infrastructure Security Laboratory (SIIS) Page 9
Building Process compiling linking loading Systems and Internet Infrastructure Security Laboratory (SIIS) Page 10
Copy Relocation data Hi, I am the linker. Oops, foo is actually defined in a different image. How can I resolve the reference to foo? GOT code <main>: ... mov $0x64,offset_to_foo(%rip) ... executable Systems and Internet Infrastructure Security Laboratory (SIIS) Page 11
Copy Relocation data Let me allocate a local copy of foo and have the dynamic loader to relocate the original variable to this new copy. GOT code <main>: ... mov $0x64,offset_to_foo(%rip) ... executable Systems and Internet Infrastructure Security Laboratory (SIIS) Page 11
Copy Relocation data Let me allocate a local copy of foo and have the dynamic foo = 0 loader to relocate the original variable to this new copy. GOT code <main>: ... mov $0x64,0x200970(%rip) ... executable Systems and Internet Infrastructure Security Laboratory (SIIS) Page 11
Building Process compiling linking loading Systems and Internet Infrastructure Security Laboratory (SIIS) Page 12
Copy Relocation data data foo = 0 GOT address of foo GOT rodata foo = 10 code code <main>: ... mov $0x64,0x200970(%rip) ... executable library Systems and Internet Infrastructure Security Laboratory (SIIS) Page 13
Copy Relocation data data foo = 0 GOT address of foo GOT rodata foo = 10 code code <main>: ... mov $0x64,0x200970(%rip) ... executable library Systems and Internet Infrastructure Security Laboratory (SIIS) Page 13
Copy Relocation data data foo = 10 GOT address of foo GOT rodata foo = 10 code code <main>: ... mov $0x64,0x200970(%rip) ... executable library Systems and Internet Infrastructure Security Laboratory (SIIS) Page 13
Copy Relocation data data foo = 10 GOT address of foo GOT rodata foo = 10 code code <main>: ... mov $0x64,0x200970(%rip) ... executable library Systems and Internet Infrastructure Security Laboratory (SIIS) Page 13
Copy Relocation Violation data data foo = 10 GOT address of foo GOT rodata foo = 10 code code <main>: ... mov $0x64,0x200970(%rip) ... executable library Systems and Internet Infrastructure Security Laboratory (SIIS) Page 13
Security Concerns • Expose “read-only” data to memory corruption attacks ‣ Making C++ vtables mutable can break existing defenses • VTV, Interleaving, SafeDispatch ‣ Making format string writable can enable printf-oriented programming • Printf-oriented programming requires mutable format string to implement branching ‣ File names ‣ IP addresses ‣ ... Systems and Internet Infrastructure Security Laboratory (SIIS) Page 14
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.