1
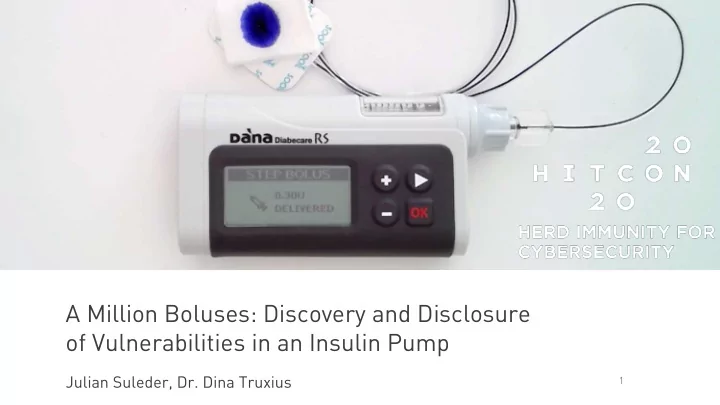
A Million Boluses: Discovery and Disclosure
- f Vulnerabilities in an Insulin Pump
A Million Boluses: Discovery and Disclosure of Vulnerabilities in an - - PowerPoint PPT Presentation
A Million Boluses: Discovery and Disclosure of Vulnerabilities in an Insulin Pump Julian Suleder, Dr. Dina Truxius 1 About Us Julian Suleder o Security Analyst & Researcher o ERNW Research GmbH o jsuleder@ernw.de o Twitter:
1
2
3
4
5
6
7
See: Council Directive 93/42/EEC of 14 June 1993 concerning medical devices
8
Photo by Jair Lázaro on Unsplash
9
[https://www.bsi.bund.de/SharedDocs/Downloads/DE/BSI/Publikationen/Lageberichte/Lagebericht2019.pdf?__blob=publicationFile&v=7, July 28, 2020]
10
11
12
13 13
14
15
16
17 17
18
Conrm Pairing on Pmp Ii P Mbie A Aderiemen \01\00<edaced> \02\00OK \01\D1 \02\D1\00 Encrp Meage ih D_KEY Calclae D_KEY from Local_Name Reqe Pairing
19
20
Conrm Pairing on Pmp I
\01\01 \02\01130816152125861D Erac P_KEY Erac S_KEY + PIN Encrp Messages ih D_KEY, P_KEY, S_KEY \002\0D23837 \A1\02 \B2\0200F21C1027E4...
21
Inlin Pm Mbile A Adeiemen \01\00<edaced> \02\00OK \01\D0\38\37 \02\D0\00 \01\01 \02\01\13\08\16\15\21\25\86\1D Enc Meage ih D_KEY Eac S_KEY + PIN Enc Meage ih D_KEY, P_KEY, S_KEY Calclae D_KEY fm Lcal_Name \A1\02 \B2\02\00\F2\1C\10\27\E4... Send P_KEY
22 22
23
24
25
26
27
28
29
Inlin Pm Mbile A Adeiemen \01\00<edaced> \02\00OK \01\D0\38\37 \02\D0\00 \01\01 \02\01\13\08\16\15\21\25\86\1D Enc Meage ih D_KEY Eac S_KEY + PIN Enc Meage ih D_KEY, P_KEY, S_KEY Calclae D_KEY fm Lcal_Name \A1\02 \B2\02\00\F2\1C\10\27\E4... Send P_KEY
30 30
31
32
33
34
[https://advancedtherapeutics.org.uk/wp-content/uploads/2020/03/User-FSN-DANA-RS-Cybersecurity-002-6-March-2020.pdf, accessed July 28,2020]
35 35
36
37
38 38
39
40
41
E-Mail: dina.truxius@bsi.bund.de Referat DI 24 Federal Office for Information Security (BSI) Godesberger Allee 185-189 53175 Bonn Germany
E-Mail: jsuleder@ernw.de Twitter: @jsuleder ERNW Research GmbH Carl-Bosch-Str. 4 69115 Heidelberg Germany