1
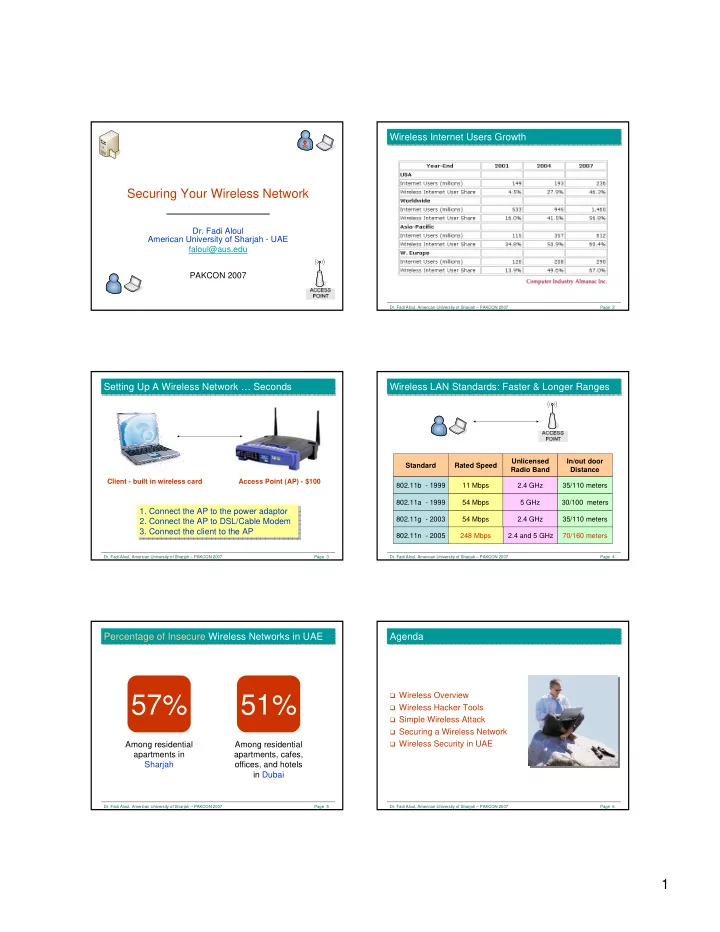
Securing Your Wireless Network
- Dr. Fadi Aloul
American University of Sharjah - UAE faloul@aus.edu PAKCON 2007
- Dr. Fadi Aloul, American University of Sharjah – PAKCON 2007
Page 2
Wireless Internet Users Growth Wireless Internet Users Growth
- Dr. Fadi Aloul, American University of Sharjah – PAKCON 2007
Page 3
Setting Up A Wireless Network … Seconds Setting Up A Wireless Network … Seconds
Access Point (AP) - $100 Client - built in wireless card
- 1. Connect the AP to the power adaptor
- 2. Connect the AP to DSL/Cable Modem
- 3. Connect the client to the AP
- 1. Connect the AP to the power adaptor
- 2. Connect the AP to DSL/Cable Modem
- 3. Connect the client to the AP
- Dr. Fadi Aloul, American University of Sharjah – PAKCON 2007
Page 4
Wireless LAN Standards: Faster & Longer Ranges Wireless LAN Standards: Faster & Longer Ranges
Standard Rated Speed Unlicensed Radio Band In/out door Distance 802.11b - 1999 11 Mbps 2.4 GHz 35/110 meters 802.11a - 1999 54 Mbps 5 GHz 30/100 meters 802.11g - 2003 54 Mbps 2.4 GHz 35/110 meters 802.11n - 2005 248 Mbps 2.4 and 5 GHz 70/160 meters
- Dr. Fadi Aloul, American University of Sharjah – PAKCON 2007
Page 5
Percentage of Insecure Wireless Networks in UAE Percentage of Insecure Wireless Networks in UAE
57%
Among residential apartments in Sharjah
51%
Among residential apartments, cafes,
- ffices, and hotels
in Dubai
- Dr. Fadi Aloul, American University of Sharjah – PAKCON 2007
Page 6
Agenda Agenda
Wireless Overview Wireless Hacker Tools Simple Wireless Attack Securing a Wireless Network Wireless Security in UAE