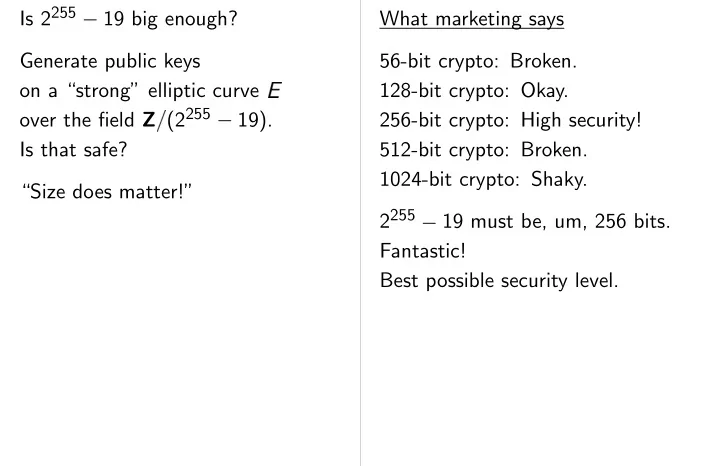
SLIDE 1 Is 2255
Generate public keys
- n a “strong” elliptic curve
- ver the field Z (2255
- 19).
Is that safe? “Size does matter!” What marketing says 56-bit crypto: Broken. 128-bit crypto: Okay. 256-bit crypto: High security! 512-bit crypto: Broken. 1024-bit crypto: Shaky. 2255
- 19 must be, um, 256 bits.
Fantastic! Best possible security level.

SLIDE 2
keys elliptic curve (2255
matter!” What marketing says 56-bit crypto: Broken. 128-bit crypto: Okay. 256-bit crypto: High security! 512-bit crypto: Broken. 1024-bit crypto: Shaky. 2255
- 19 must be, um, 256 bits.
Fantastic! Best possible security level. What NSA says NSA approves products “classified or mission national security info NSA wants “elliptic GF( ), where is greater than 2255.” So 2255 + 95 is fine for national securit but 2255

SLIDE 3 What marketing says 56-bit crypto: Broken. 128-bit crypto: Okay. 256-bit crypto: High security! 512-bit crypto: Broken. 1024-bit crypto: Shaky. 2255
- 19 must be, um, 256 bits.
Fantastic! Best possible security level. What NSA says NSA approves products for “classified or mission critical national security information.” NSA wants “elliptic curves over GF( ), where is a prime number greater than 2255.” So 2255 + 95 is fine for national security information but 2255

SLIDE 4 says Broken. Okay. High security! Broken. Shaky.
security level. What NSA says NSA approves products for “classified or mission critical national security information.” NSA wants “elliptic curves over GF( ), where is a prime number greater than 2255.” So 2255 + 95 is fine for national security information but 2255
What NIST says 128-bit AES keys “co ECC primes with “256-383” the amount of work “break the algorithms” is approximately the namely 2128 operations, by best techniques

SLIDE 5 What NSA says NSA approves products for “classified or mission critical national security information.” NSA wants “elliptic curves over GF( ), where is a prime number greater than 2255.” So 2255 + 95 is fine for national security information but 2255
What NIST says 128-bit AES keys “correspond” to ECC primes with “256-383” bits: the amount of work needed to “break the algorithms” is approximately the same, namely 2128 operations, by best techniques known.

SLIDE 6 roducts for mission critical information.” “elliptic curves over is a prime number .” fine security information
What NIST says 128-bit AES keys “correspond” to ECC primes with “256-383” bits: the amount of work needed to “break the algorithms” is approximately the same, namely 2128 operations, by best techniques known. What I say Given ( ) = AES
2127 AES Given ( 1)
✁
( 2
✁ ✂ ✂ ✂ ✁
find all
✄ using a
AES evaluations. Or find some
✄ using
evaluations. Standard algorithms negligible communication perfect parallelization: cr.yp.to/papers.html #bruteforce

SLIDE 7
What NIST says 128-bit AES keys “correspond” to ECC primes with “256-383” bits: the amount of work needed to “break the algorithms” is approximately the same, namely 2128 operations, by best techniques known. What I say Given ( ) = AES
(0), find
using 2127 AES evaluations. Given ( 1)
✁
( 2)
✁ ✂ ✂ ✂ ✁
( 240), find all
✄ using a total of
2127 AES evaluations. Or find some
✄ using
287 AES evaluations. Standard algorithms have negligible communication and perfect parallelization: see, e.g., cr.yp.to/papers.html #bruteforce

SLIDE 8 eys “correspond” to “256-383” bits:
rithms” the same, erations, techniques known. What I say Given ( ) = AES
(0), find
using 2127 AES evaluations. Given ( 1)
✁
( 2)
✁ ✂ ✂ ✂ ✁
( 240), find all
✄ using a total of
2127 AES evaluations. Or find some
✄ using
287 AES evaluations. Standard algorithms have negligible communication and perfect parallelization: see, e.g., cr.yp.to/papers.html #bruteforce Given public key on 255-bit elliptic curve find secret key using 2127 additions Given 240 public keys, find all secret keys using 2147 additions Finding some key is as finding first key: 2127 additions. Easily by random self-reduction. See, e.g., Kuhn and

SLIDE 9
What I say Given ( ) = AES
(0), find
using 2127 AES evaluations. Given ( 1)
✁
( 2)
✁ ✂ ✂ ✂ ✁
( 240), find all
✄ using a total of
2127 AES evaluations. Or find some
✄ using
287 AES evaluations. Standard algorithms have negligible communication and perfect parallelization: see, e.g., cr.yp.to/papers.html #bruteforce Given public key on 255-bit elliptic curve , find secret key using 2127 additions on . Given 240 public keys, find all secret keys using 2147 additions on . Finding some key is as hard as finding first key: 2127 additions. Easily prove by random self-reduction. See, e.g., Kuhn and Struik, 2001.

SLIDE 10 AES
(0), find
AES evaluations.
✁
2)
✁ ✂ ✂ ✂ ✁
( 240),
✄
a total of 2127 evaluations.
✄ using
287 AES rithms have communication and rallelization: see, e.g., cr.yp.to/papers.html Given public key on 255-bit elliptic curve , find secret key using 2127 additions on . Given 240 public keys, find all secret keys using 2147 additions on . Finding some key is as hard as finding first key: 2127 additions. Easily prove by random self-reduction. See, e.g., Kuhn and Struik, 2001. Even worse for AES: can try much less computation. Success chance drops For elliptic curves, drops quadratically Bottom line: 128-bit not comparable in to 255-bit elliptic-curve Is 2255
Is 128-bit AES safe?

SLIDE 11 Given public key on 255-bit elliptic curve , find secret key using 2127 additions on . Given 240 public keys, find all secret keys using 2147 additions on . Finding some key is as hard as finding first key: 2127 additions. Easily prove by random self-reduction. See, e.g., Kuhn and Struik, 2001. Even worse for AES: Attacker can try much less computation. Success chance drops linearly. For elliptic curves, success chance drops quadratically. Bottom line: 128-bit AES keys are not comparable in security to 255-bit elliptic-curve keys. Is 2255
Is 128-bit AES safe? Unclear.