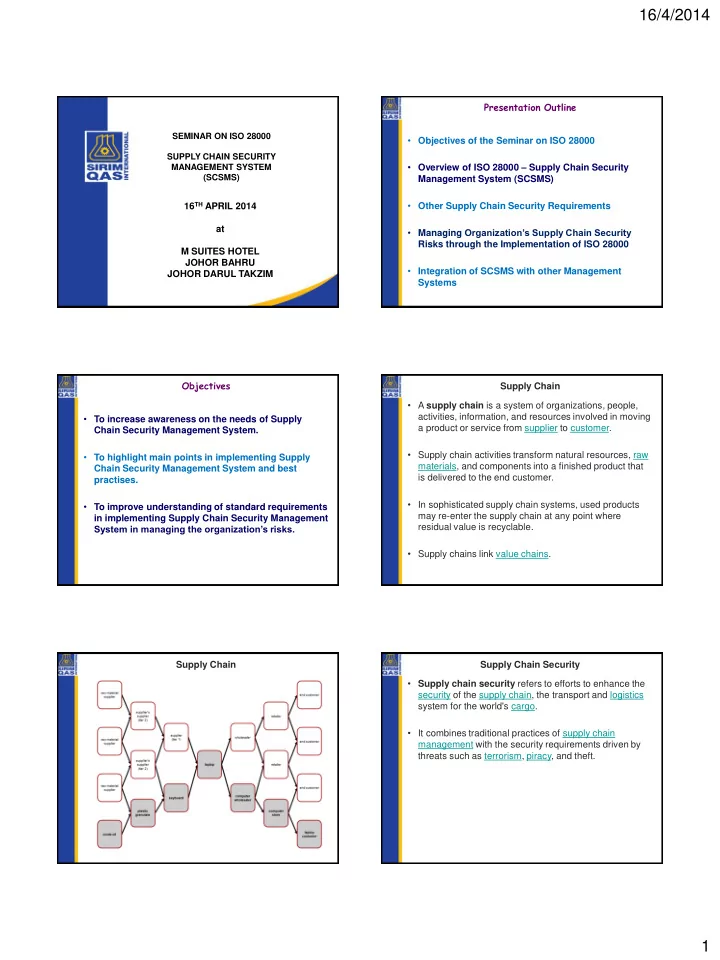
SLIDE 1
16/4/2014 1
16TH APRIL 2014 at M SUITES HOTEL JOHOR BAHRU JOHOR DARUL TAKZIM
SEMINAR ON ISO 28000 SUPPLY CHAIN SECURITY MANAGEMENT SYSTEM (SCSMS)
Presentation Outline
- Objectives of the Seminar on ISO 28000
- Overview of ISO 28000 – Supply Chain Security
Management System (SCSMS)
- Other Supply Chain Security Requirements
- Managing Organization’s Supply Chain Security
Risks through the Implementation of ISO 28000
- Integration of SCSMS with other Management
Systems Objectives
- To increase awareness on the needs of Supply
Chain Security Management System.
- To highlight main points in implementing Supply
Chain Security Management System and best practises.
- To improve understanding of standard requirements
in implementing Supply Chain Security Management System in managing the organization’s risks. Supply Chain
- A supply chain is a system of organizations, people,
activities, information, and resources involved in moving a product or service from supplier to customer.
- Supply chain activities transform natural resources, raw
materials, and components into a finished product that is delivered to the end customer.
- In sophisticated supply chain systems, used products
may re-enter the supply chain at any point where residual value is recyclable.
- Supply chains link value chains.
Supply Chain Supply Chain Security
- Supply chain security refers to efforts to enhance the
security of the supply chain, the transport and logistics system for the world's cargo.
- It combines traditional practices of supply chain