11/24/2009 1
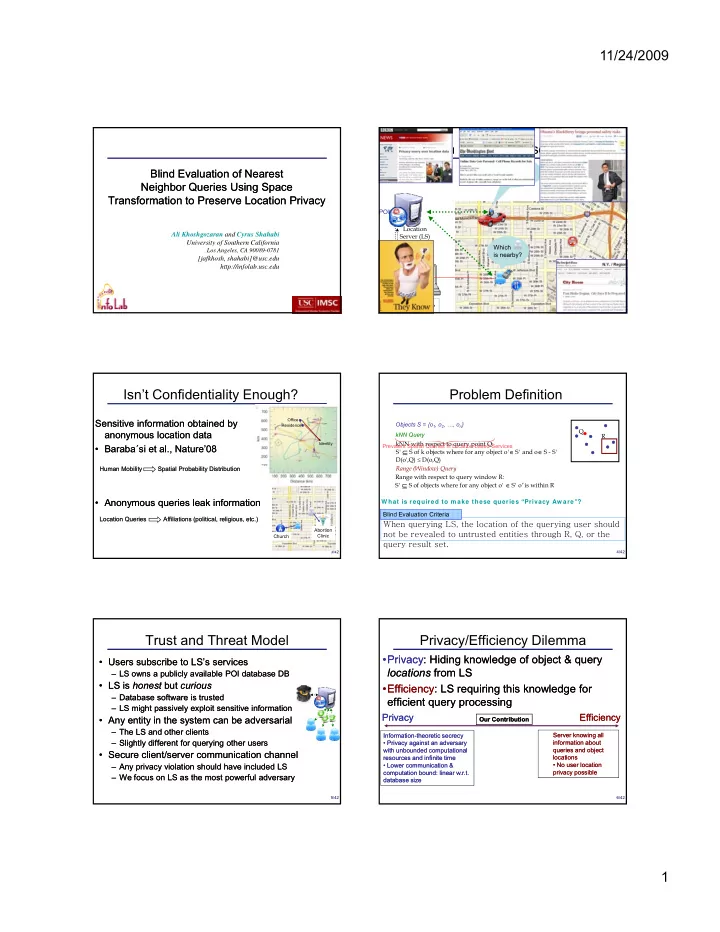
Blind Evaluation of Nearest Blind Evaluation of Nearest Neighbor Queries Using Space Neighbor Queries Using Space Transformation to Preserve Location Privacy Transformation to Preserve Location Privacy
Ali Khoshgozaran and Cyrus Shahabi University of Southern California
Los Angeles, CA 90089-0781
[jafkhosh, shahabi]@usc.edu http://infolab.usc.edu
Privacy in Location Based Services
POI Where's the nearest ?
2 /42
Which is nearby?
Motivation Motivation Problem Definition Problem Definition Related Work Related Work Introduction Introduction Our Work Our Work Proposed Work Proposed Work
Location Server (LS)
Sensitive information obtained by Sensitive information obtained by anonymous location data anonymous location data
- Baraba
Baraba´ ´si et al., Nature’08 si et al., Nature’08
Isn’t Confidentiality Enough?
Office Residence Identity 3 /42
- Anonymous queries leak information
Anonymous queries leak information
Location Queries Affiliations (political, religious, etc.) Location Queries Affiliations (political, religious, etc.) Human Mobility Spatial Probability Distribution Human Mobility Spatial Probability Distribution
Church Abortion Clinic
Objects S = {o1, o2, …, on} kNN Query kNN with respect to query point Q: S' ⊆ S of k objects where for any object o'∈ S' and o∈ S - S' D(o',Q) ≤ D(o,Q)
Problem Definition
Q R
Prevalent Spatial Queries in Location-based Services
4 /42
W hat is required to m ake these queries “Privacy Aw are”? Range with respect to query window R: S' ⊆ S of objects where for any object o' ∈ S' o' is within R
When querying LS, the location of the querying user should not be revealed to untrusted entities through R, Q, or the query result set.
Blind Evaluation Criteria Range (Window) Query
Trust and Threat Model
- Users subscribe to LS’s services
Users subscribe to LS’s services
– LS owns a publicly available POI database DB LS owns a publicly available POI database DB
- LS is
LS is honest honest but but curious curious
– Database software is trusted Database software is trusted – LS might passively exploit sensitive information LS might passively exploit sensitive information
5 /42
g p y p g p y p
- Any entity in the system can be adversarial
Any entity in the system can be adversarial
– The LS and other clients The LS and other clients – Slightly different for querying other users Slightly different for querying other users
- Secure client/server communication channel
Secure client/server communication channel
– Any privacy violation should have included LS Any privacy violation should have included LS – We focus on LS as the most powerful adversary We focus on LS as the most powerful adversary
Privacy/Efficiency Dilemma
- Privacy
Privacy: Hiding knowledge of object & query : Hiding knowledge of object & query locations locations from LS from LS
- Efficiency
Efficiency: LS requiring this knowledge for : LS requiring this knowledge for efficient query processing efficient query processing
6 /42
Server knowing all Server knowing all information about information about queries and object queries and object locations locations
- No user location
No user location privacy possible privacy possible
Privacy Privacy Efficiency Efficiency
Information Information-
- theoretic secrecy
theoretic secrecy
- Privacy against an adversary
Privacy against an adversary with unbounded computational with unbounded computational resources and infinite time resources and infinite time
- Lower communication &
Lower communication & computation bound: linear w.r.t. computation bound: linear w.r.t. database size database size Our Contribution Our Contribution