Object-Oriented Software Engineering
Practical Software Development using UML and Java Chapter 10: Testing and Inspecting to Ensure High Quality
!"#$%&'()*+$,#-+-.)/($"0112
3&-4%$("215"6$7%).+"-.*"8.74$9%).+":;("<)+&"=>-?)%@
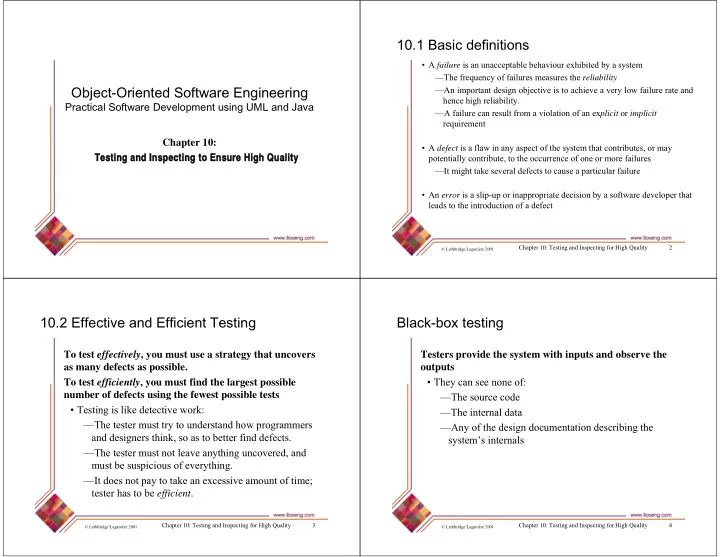
10.1 Basic definitions
A B"failure )7"-.">.-99$4%-'?$"'$&-C);>("$D&)')%$*"'@"-"7@7%$E F6&$":($G>$.9@";:":-)?>($7"E$-7>($7"%&$"reliability FB.")E4;(%-.%"*$7)+.";'H$9%)C$")7"%;"-9&)$C$"-"C$(@"?;I":-)?>($"(-%$"-.*" &$.9$"&)+&"($?)-')?)%@J FB":-)?>($"9-."($7>?%":(;E"-"C);?-%);.";:"-."$Dplicit ;( implicit ($G>)($E$.% A B"defect )7"-":?-I")."-.@"-74$9%";:"%&$"7@7%$E"%&-%"9;.%()'>%$7K";("E-@" 4;%$.%)-??@"9;.%()'>%$K"%;"%&$";99>(($.9$";:";.$";("E;($":-)?>($7 F8%"E)+&%"%-L$"7$C$(-?"*$:$9%7"%;"9->7$"-"4-(%)9>?-(":-)?>($ A B."error )7"-"7?)4M>4";(").-44(;4()-%$"*$9)7);."'@"-"7;:%I-($"*$C$?;4$("%&-%" ?$-*7"%;"%&$").%(;*>9%);.";:"-"*$:$9%"
!"#$%&'()*+$,#-+-.)/($"0112
3&-4%$("215"6$7%).+"-.*"8.74$9%).+":;("<)+&"=>-?)%@ N
10.2 Effective and Efficient Testing
To test effectively, you must use a strategy that uncovers as many defects as possible. To test efficiently, you must find the largest possible number of defects using the fewest possible tests A 6$7%).+")7"?)L$"*$%$9%)C$"I;(L5 F6&$"%$7%$("E>7%"%(@"%;">.*$(7%-.*"&;I"4(;+(-EE$(7"
- .*"*$7)+.$(7"%&).LK"7;"-7"%;"'$%%$(":).*"*$:$9%7J
F6&$"%$7%$("E>7%".;%"?$-C$"-.@%&).+">.9;C$($*K"-.*" E>7%"'$"7>74)9);>7";:"$C$(@%&).+J F8%"*;$7".;%"4-@"%;"%-L$"-."$D9$77)C$"-E;>.%";:"%)E$O" %$7%$("&-7"%;"'$"efficientJ
!"#$%&'()*+$,#-+-.)/($"0112
3&-4%$("215"6$7%).+"-.*"8.74$9%).+":;("<)+&"=>-?)%@ P
Black-box testing
Testers provide the system with inputs and observe the
- utputs