1
Fall 2008 CS 334: Computer Security Slide #1
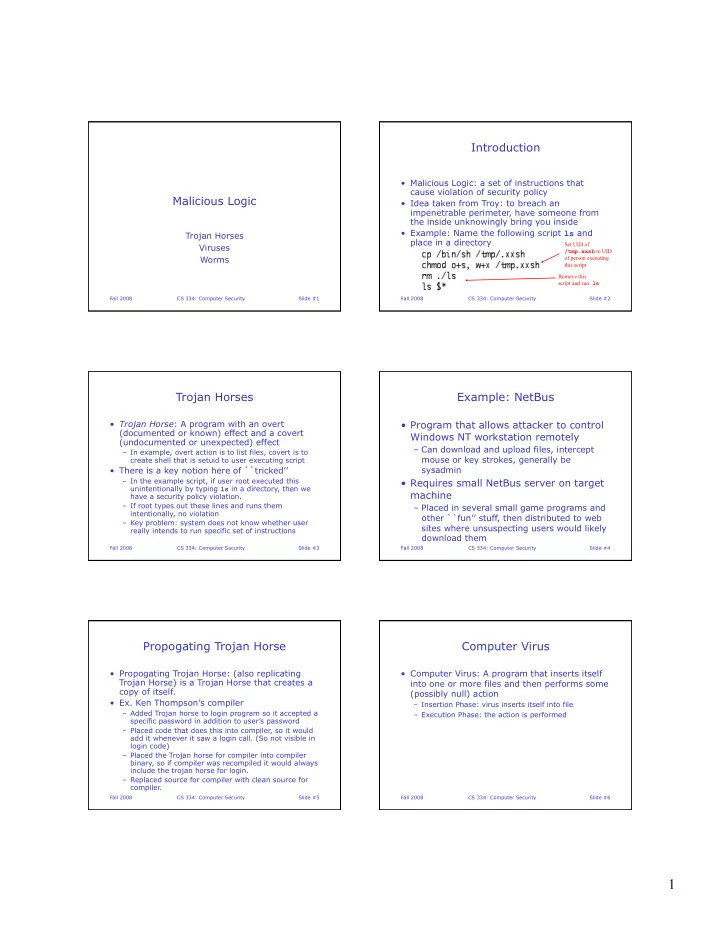
Malicious Logic
Trojan Horses Viruses Worms
Fall 2008 CS 334: Computer Security Slide #2
Introduction
- Malicious Logic: a set of instructions that
cause violation of security policy
- Idea taken from Troy: to breach an
impenetrable perimeter, have someone from the inside unknowingly bring you inside
- Example: Name the following script ls and
place in a directory
Set UID of /tmp.xxsh to UID
- f person executing
this script Remove this script and run ls
Fall 2008 CS 334: Computer Security Slide #3
Trojan Horses
- Trojan Horse: A program with an overt
(documented or known) effect and a covert (undocumented or unexpected) effect
– In example, overt action is to list files, covert is to create shell that is setuid to user executing script
- There is a key notion here of ``tricked’’
– In the example script, if user root executed this unintentionally by typing ls in a directory, then we have a security policy violation. – If root types out these lines and runs them intentionally, no violation – Key problem: system does not know whether user really intends to run specific set of instructions
Fall 2008 CS 334: Computer Security Slide #4
Example: NetBus
- Program that allows attacker to control
Windows NT workstation remotely
– Can download and upload files, intercept mouse or key strokes, generally be sysadmin
- Requires small NetBus server on target
machine
– Placed in several small game programs and
- ther ``fun’’ stuff, then distributed to web
sites where unsuspecting users would likely download them
Fall 2008 CS 334: Computer Security Slide #5
Propogating Trojan Horse
- Propogating Trojan Horse: (also replicating
Trojan Horse) is a Trojan Horse that creates a copy of itself.
- Ex. Ken Thompson’s compiler
– Added Trojan horse to login program so it accepted a specific password in addition to user’s password – Placed code that does this into compiler, so it would add it whenever it saw a login call. (So not visible in login code) – Placed the Trojan horse for compiler into compiler binary, so if compiler was recompiled it would always include the trojan horse for login. – Replaced source for compiler with clean source for compiler.
Fall 2008 CS 334: Computer Security Slide #6
Computer Virus
- Computer Virus: A program that inserts itself