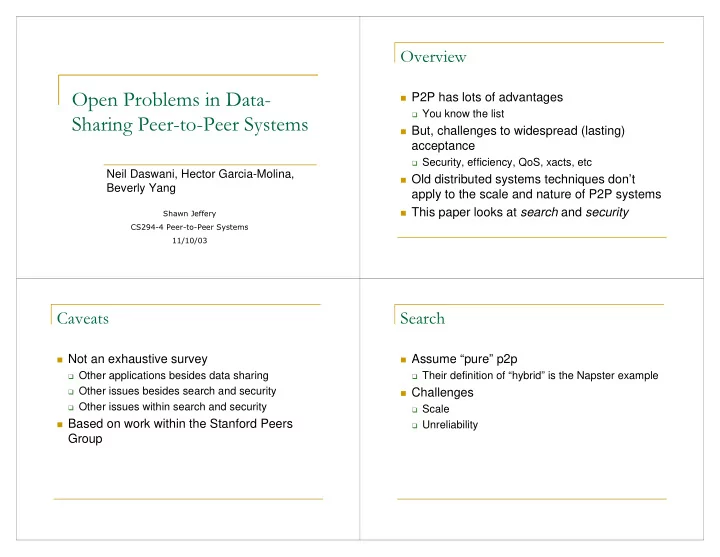
- Neil Daswani, Hector Garcia-Molina,
Beverly Yang
- P2P has lots of advantages
You know the list
But, challenges to widespread (lasting)
acceptance
Security, efficiency, QoS, xacts, etc
Old distributed systems techniques don’t
apply to the scale and nature of P2P systems
This paper looks at search and security
- Not an exhaustive survey
Other applications besides data sharing Other issues besides search and security Other issues within search and security
Based on work within the Stanford Peers
Group
- Assume “pure” p2p
Their definition of “hybrid” is the Napster example
Challenges
Scale Unreliability