SAC
Su
mmer
Sch
Can
Crypto Enhance
Democracy
Part
I
Clerk
Concordia University
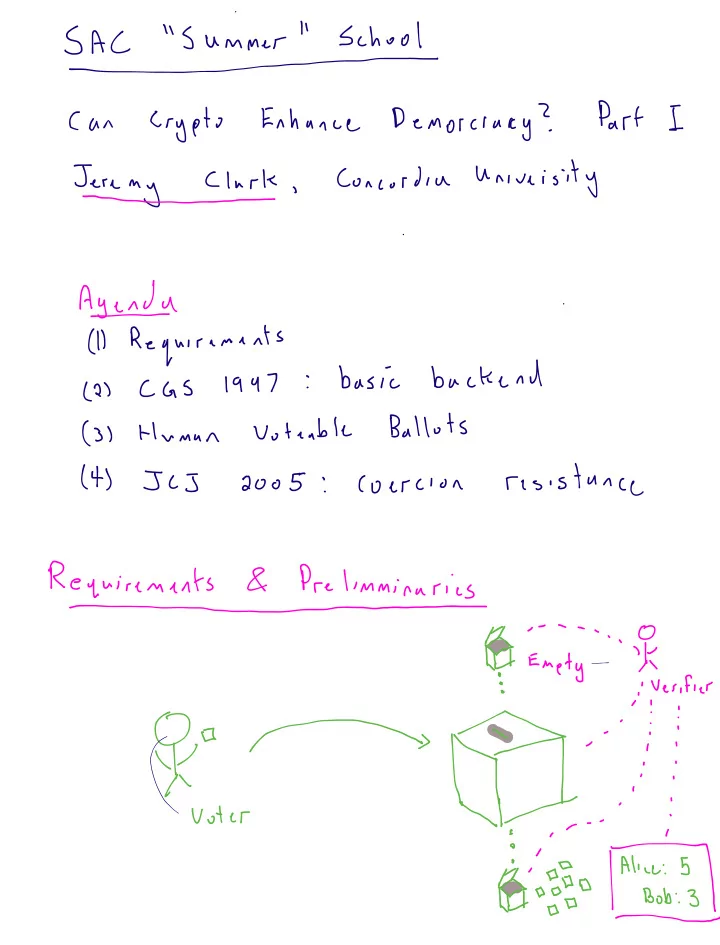
Agenda
1
Requirements
2
CGS 1947
basic
backend
3
Human
Votiable
Ballots
t JCJ
2005 Coercion
resistance
Requirements
Preliminaries
Enety
Fi
i Verify
i
Oo
ii
Wi
Voter
i
iii opium
Bob
3_