1 IT Security Evaluation
Simone Fischer-Hübner
Why do we need security evaluation
To provide a basis for specifying security
expectations
To verify that a computer product/system
fulfills the requirements imposed on it
To establish a metric for the degree of trust
that can be placed on a security product/system (“objective yardstick”)
To guide developers which security is expected To fulfil legal requirements (§ 14 German
Digital Signature Act, § 17 Digital Signature Ordinance)
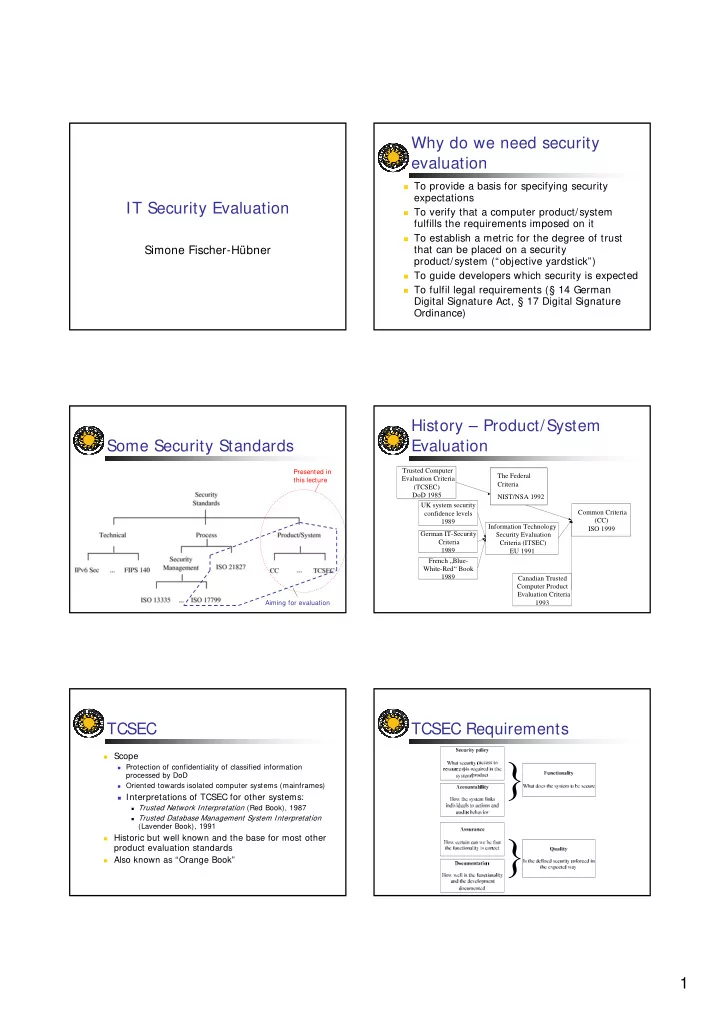
Some Security Standards
Aiming for evaluation Presented in this lecture
History – Product/System Evaluation
Trusted Computer Evaluation Criteria (TCSEC) DoD 1985 Information Technology Security Evaluation Criteria (ITSEC) EU 1991 UK system security confidence levels 1989 German IT-Security Criteria 1989 French „Blue- White-Red“ Book 1989 Canadian Trusted Computer Product Evaluation Criteria 1993 Common Criteria (CC) ISO 1999 The Federal Criteria NIST/NSA 1992
TCSEC
Scope
Protection of confidentiality of classified information
processed by DoD
Oriented towards isolated computer systems (mainframes)
Interpretations of TCSEC for other systems:
Trusted Network Interpretation (Red Book), 1987 Trusted Database Management System Interpretation
(Lavender Book), 1991
Historic but well known and the base for most other
product evaluation standards
Also known as “Orange Book”