Who do you Trust? The roles of certificates, certification - PowerPoint PPT Presentation
Who do you Trust? The roles of certificates, certification authorities and the IGTF in Grid Computing T h e A m e r i c a s G r i d Policy Management Authority Prof. Vinod Rebello Instituto de Computao Universidade F ederal F
Who do you Trust? The roles of certificates, certification authorities and the IGTF in Grid Computing T h e A m e r i c a s G r i d Policy Management Authority Prof. Vinod Rebello Instituto de Computação Universidade F ederal F luminense Brazil vinod@ic.uff.br
A talk about PKI - Why me? • Resource provider and grid operator and user • Manager of the IGTF approved Brazilian and the Latin American and Caribbean Catch-all Grid Certificate Authorities • Current Chair of the TAGPMA • Former Chair of the IGTF There is are worlds outside of Grid Computing… • Chair of the Brazilian Educational PMA (ICPEDU) • Brazilian Federal PKI Service And these worlds are colliding! I I LA Grid W orkshop 2 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
The Grid Computing Model In this generic model, institutions and businesses own fewer of their own resources. Third parties provide facilities; users get access to services. Businesses themselves can also offer services over the Grid. Grid/Cloud offering services I I LA Grid W orkshop 3 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
Role of Computer Security • Confidentiality : protection against data disclosure to unauthorized persons • I ntegrity : protection against data modification • Availability : protection against data disponibility • I dentification & Authentication (I&A) – Provide a way of identifying entities, and controlling this identity • Non-repudiability – Bind an entity to its actions • Authorization – Identity combined with an access policy to grant rights to perform some action I I LA Grid W orkshop 4 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
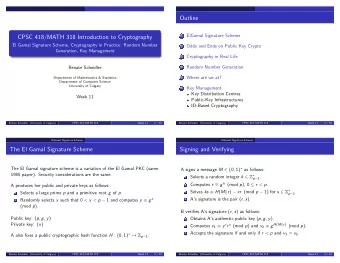
Asymmetric Cryptography • Use non-reversible functions and a key pair – What one key encrypts, the other decrypts • Keep one key private pub – Only you can decrypt Hello $w!4& F(x) • Let the other be public – Everyone can encrypt priv • Security relies on – F -1 not being found $w!4& Hello F(x) I I LA Grid W orkshop 5 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
Assymetric Key Pairs • Every user splits a key pair into a private and a public key. priv pub The public key is known The private key should not by everybody. be known by anyone else. It may be protected by hardware. I I LA Grid W orkshop 6 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
X.509 Public Key Certificate • A standardised way to associate a public key with an entity • A digitally signed identity document – Can identify people, computers, services, … Version Serial number Issuer identity Validity period User identity Public key Extension fields (Extension data: what type of vehicles the person is authorized to drive) I I LA Grid W orkshop 7 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
Certificates and PKIs • Certificates enable: – Clients to authenticate servers – Servers to authenticate clients – Public key exchange without Public Key Server • No disclosure of private/ secret keys. • Special features: – chains of CAs, to distribute the task of issuing certificates – Certificate Revocation List, to disable certificates • CA is the only entity able to create/ modify the certificate – the CA has to be trusted I I LA Grid W orkshop 8 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
Certification Authority • The role of the CA is to manage the certificate life cycle: create, store, renew, revoke User data CA User data Public key Trusted CA signature Third Public key Party User certificate I I LA Grid W orkshop 9 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
Establishing Trust • The dynamic cross-organizational resource sharing gives us a problem – No initial trust, different policies, different mechanisms – no central point of control in Grids • We have to provide tools to make this as painless as possible I I LA Grid W orkshop 1 0 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
Solving the Trust Problem • Trusted Third Parties – Independent identity assessment providers – The most commonly used today • Federations – Organizations trust each other to identify their own users – Finite “membership” constellations • Web of Trust – Users trust each other to identify others – Less control, scalability arguable I I LA Grid W orkshop 1 1 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
International Grid Trust Fed. • Commissioned: Mar 2003 (Tokyo) - Chartered: October 5 th , 2005 at GGF 16 (Chicago) • Federation of European, Asian, and Western Hemisphere Policy Management Authorities – Focused on Identity management and authentication for Grids • Establishment of top level CA registries and related services – Root CA certificates, CA repositories and CRL publishing points. – Uses TERENA Academic CA Repository (TACAR) • Standards – Certificate policies, Certificate profiles, Accreditation – Open Grid Forum publishes standards and community best practices. I I LA Grid W orkshop 1 2 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
Building the Federation • Resource Providers and Relying Parties together shape the common minimum requirements – Several profiles for different identity management models • different technologies – Authorities testify to compliance with profile guidelines – Peer-review process within the federation to (re) evaluate members on entry & periodically – Reduce effort on the relying parties • single document to review and assess for all Authorities • collective acceptance of all accredited authorities – Reduce cost on the authorities • but participation in the federation comes with a price • … the ultimate decision always remains with the RP • Policies are technology independent I I LA Grid W orkshop 1 3 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
The Regional PMAs The Americas Grid European Grid Asia Pacific PMA PMA Grid PMA I I LA Grid W orkshop 1 4 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
TAGPMA Membership CANARI E – Canada DOEGrids ( ESNet) – USA EELA – I nternational Ferm i National Accelerator Laboratory - USA HEBCA/ USHER/ Dartm outh College – USA I BDS ( ANSP) - Brazil LCG – I nternational NCSA – USA NERSC – USA Open Science Grid – I nternational Purdue University – USA REUNA – Chile San Diego Supercom puter Center – USA TACC – USA TeraGrid – USA Texas High Energy Grid – USA University of Virginia – USA UFF – Brazil ULA – Venezuela I GTF Accredited CA Operators UNAM – Mexico CA Accreditation in progress UNLP – Argentina I nterested in accreditation Relying Party I I LA Grid W orkshop 1 5 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
What Are Grid PKIs For? • Exist to serve the grid community in terms of authentication – X.509 certificates are an essential component of Grid security mechanisms – Authentication supports diverse authorization methods (including ongoing research) – X.509 Certification Authorities provide a focal point for policy and key lifecycle management – IGTF and regional PMAs provide coordination and interoperability standards for Grid PKIs I I LA Grid W orkshop 1 6 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
Fostering NGIs in LA? • Fostering National Grid Initiatives to meet the demands of Latin America – Not just computer science, nor is it just e-science, its e-verything! – Learn from but not necessarily copy other NGIs • Sustainability – Maintenance support for large scale, production class infrastructures – Tools to improve accessibility – More users – Integrate Grid PKI with other broader scoped PKIs • UFF BrGrid CA will be an integral part of the Brazilian Educational and Research PKI (ICPEDU). I I LA Grid W orkshop 1 7 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
Contact Information • Argentinean National Grid CA – UNLP Grid CA http: / / www.pkiunlpgrid.unlp.edu.ar • Brazilian National Grid CA – UFF BrGrid CA http: / / brgrid.ic.uff.br • Chilean National Grid CA – REUNA CA http: / / reuna-ca.reuna.cl • Latin American and Caribbean Catch-all CA – UFF LACGrid CA http: / / lacgridca.ic.uff.br • TAGPMA http: / / www.tagpma.org • Questions? • My email – vinod@ic.uff.br I I LA Grid W orkshop 1 8 3 0 th Oct 2 0 0 8 Vinod Rebello – vinod@ic.uff.br
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.





![KEY DISTRIBUTION 1 / 74 The public key setting Bob pk [ A ] Alice C $ M D sk [ A ] (](https://c.sambuz.com/863704/key-distribution-s.webp)