SLIDE 1 Understanding brute force
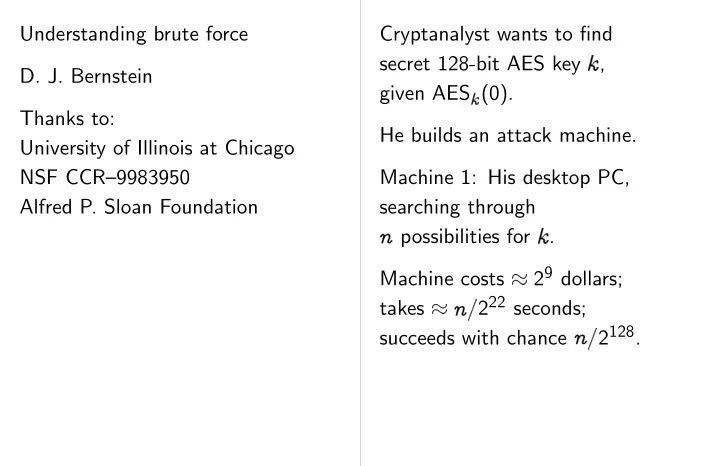
Thanks to: University of Illinois at Chicago NSF CCR–9983950 Alfred P. Sloan Foundation Cryptanalyst wants to find secret 128-bit AES key , given AES
(0).
He builds an attack machine. Machine 1: His desktop PC, searching through
✁
possibilities for . Machine costs 29 dollars; takes
✁
222 seconds; succeeds with chance
✁
2128.

SLIDE 2 rute force Illinois at Chicago CCR–9983950 Foundation Cryptanalyst wants to find secret 128-bit AES key , given AES
(0).
He builds an attack machine. Machine 1: His desktop PC, searching through
✁
possibilities for . Machine costs 29 dollars; takes
✁
222 seconds; succeeds with chance
✁
2128. This is a silly attack The cryptanalyst has Machine 2: desktop each searching through
✁
possibilities for Machine costs 2 takes
✁
222 seconds; succeeds with chance
✁
Same keys/dollar-second: Same chance/dolla

SLIDE 3
Cryptanalyst wants to find secret 128-bit AES key , given AES
(0).
He builds an attack machine. Machine 1: His desktop PC, searching through
✁
possibilities for . Machine costs 29 dollars; takes
✁
222 seconds; succeeds with chance
✁
2128. This is a silly attack machine. The cryptanalyst has more money. Machine 2: desktop PCs, each searching through
✁
possibilities for . Machine costs 29 dollars; takes
✁
222 seconds; succeeds with chance
✁
2128. Same keys/dollar-second: 213. Same chance/dollar-second: 2
115.
But larger chance!

SLIDE 4 ants to find AES key ,
desktop PC, through
✁
r . 29 dollars;
✁
seconds; chance
✁
2128. This is a silly attack machine. The cryptanalyst has more money. Machine 2: desktop PCs, each searching through
✁
possibilities for . Machine costs 29 dollars; takes
✁
222 seconds; succeeds with chance
✁
2128. Same keys/dollar-second: 213. Same chance/dollar-second: 2
115.
But larger chance! This is a silly attack Only a tiny part of is doing anything useful. Machine 3: tiny each searching through
✁
possibilities for AES circuit, in bulk, is orders of magnitude less expensive than allowing much larger Cost ratio grows with Recall DES Cracker: 219 keys/dollar-second.

SLIDE 5
This is a silly attack machine. The cryptanalyst has more money. Machine 2: desktop PCs, each searching through
✁
possibilities for . Machine costs 29 dollars; takes
✁
222 seconds; succeeds with chance
✁
2128. Same keys/dollar-second: 213. Same chance/dollar-second: 2
115.
But larger chance! This is a silly attack machine. Only a tiny part of the PC is doing anything useful. Machine 3: tiny AES circuits, each searching through
✁
possibilities for . AES circuit, in bulk, is orders of magnitude less expensive than PC, allowing much larger . Cost ratio grows with PC size! Recall DES Cracker: in 1997, 219 keys/dollar-second.

SLIDE 6 attack machine. cryptanalyst has more money. desktop PCs, through
✁
r . 29 dollars;
✁
seconds; chance
✁
2128. r-second: 213. chance/dollar-second: 2
115.
chance! This is a silly attack machine. Only a tiny part of the PC is doing anything useful. Machine 3: tiny AES circuits, each searching through
✁
possibilities for . AES circuit, in bulk, is orders of magnitude less expensive than PC, allowing much larger . Cost ratio grows with PC size! Recall DES Cracker: in 1997, 219 keys/dollar-second. This is still silly if cryptanalyst is actually many keys
1
✁ ✁
Complicated but standa brute-force key-sea handles keys using rainbow tables, using distinguished Similar time, price Conjecturally
✁
distinguished points,

SLIDE 7 This is a silly attack machine. Only a tiny part of the PC is doing anything useful. Machine 3: tiny AES circuits, each searching through
✁
possibilities for . AES circuit, in bulk, is orders of magnitude less expensive than PC, allowing much larger . Cost ratio grows with PC size! Recall DES Cracker: in 1997, 219 keys/dollar-second. This is still silly if cryptanalyst is actually attacking many keys
1
✁ ✁ .
Complicated but standard parallel brute-force key-search machine handles keys at once using rainbow tables, or using distinguished points. Similar time, price to one key. Conjecturally
✁
2128 chance
distinguished points, slightly lower.

SLIDE 8 attack machine.
anything useful. tiny AES circuits, through
✁
r . bulk, magnitude than PC, rger . with PC size! Cracker: in 1997, r-second. This is still silly if cryptanalyst is actually attacking many keys
1
✁ ✁ .
Complicated but standard parallel brute-force key-search machine handles keys at once using rainbow tables, or using distinguished points. Similar time, price to one key. Conjecturally
✁
2128 chance
distinguished points, slightly lower. Is this acceptable securit If not, what do we Option 1: Input-space to stop many-keys “Use a large random Heavy costs (usually limited benefits. Option 2: Use 32-b “Randomness in key Smaller costs; larger See paper for further http://cr.yp.to /papers.html#bruteforce

SLIDE 9 This is still silly if cryptanalyst is actually attacking many keys
1
✁ ✁ .
Complicated but standard parallel brute-force key-search machine handles keys at once using rainbow tables, or using distinguished points. Similar time, price to one key. Conjecturally
✁
2128 chance
distinguished points, slightly lower. Is this acceptable security? If not, what do we do? Option 1: Input-space separation, to stop many-keys attacks. “Use a large random nonce.” Heavy costs (usually understated); limited benefits. Option 2: Use 32-byte keys. “Randomness in key, not nonce.” Smaller costs; larger benefits. See paper for further analysis: http://cr.yp.to /papers.html#bruteforce

SLIDE 10 if actually attacking
✁ ✁ .
standard parallel ey-search machine eys at once tables, or distinguished points. rice to one key.
✁
2128 chance every key;
Is this acceptable security? If not, what do we do? Option 1: Input-space separation, to stop many-keys attacks. “Use a large random nonce.” Heavy costs (usually understated); limited benefits. Option 2: Use 32-byte keys. “Randomness in key, not nonce.” Smaller costs; larger benefits. See paper for further analysis: http://cr.yp.to /papers.html#bruteforce Basic cryptanalytic A new attack is pointless it takes less time than standard brute-fo at the same price with the same success Most papers get this Example: The attack 9 rounds of 256-bit had larger price and complete brute-force through all 2256 keys.

SLIDE 11
Is this acceptable security? If not, what do we do? Option 1: Input-space separation, to stop many-keys attacks. “Use a large random nonce.” Heavy costs (usually understated); limited benefits. Option 2: Use 32-byte keys. “Randomness in key, not nonce.” Smaller costs; larger benefits. See paper for further analysis: http://cr.yp.to /papers.html#bruteforce Basic cryptanalytic economics A new attack is pointless unless it takes less time than standard brute-force machine at the same price with the same success chance. Most papers get this wrong. Example: The attack “breaking” 9 rounds of 256-bit Serpent had larger price and time than a complete brute-force search through all 2256 keys.