UK GDPR readiness survey - International Data Corporation (IDC) % - - PowerPoint PPT Presentation
UK GDPR readiness survey - International Data Corporation (IDC) % - - PowerPoint PPT Presentation
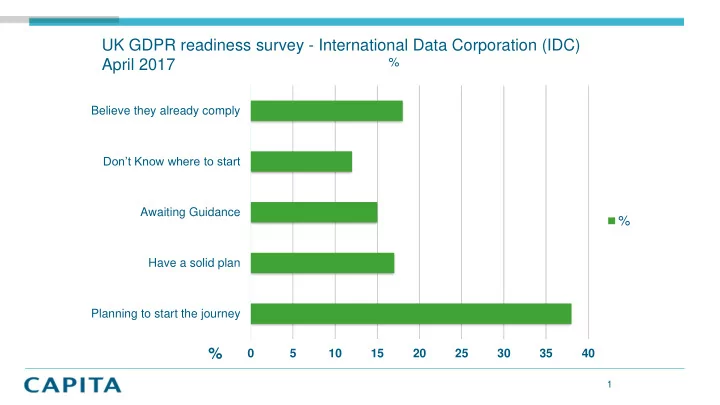
UK GDPR readiness survey - International Data Corporation (IDC) % April 2017 Believe they already comply Dont Know where to start Awaiting Guidance % Have a solid plan Planning to start the journey % 0 5 10 15 20 25 30 35 40 1
- New regulations concerning Personal Data - May 2018
- Any identifiable personal data - cookies, telematic data, IP address, bio-
metric data, CCTV
- Fines of up to 4% of gross annual turnover or €20m, whichever is greater
- Additional fines of 2% or €10m for failure to report data breaches within 72 hours
GDPR Headlines
Elizabeth Denholm (Head of UK ICO) said in a recent talk… “The new legislation creates an onus on companies to understand the risks that they create for others, and to mitigate those risks. It’s about moving away from seeing the law as a box ticking exercise, and instead to work on a framework that can be used to build a culture of privacy that pervades an entire organisation”
2
More than 200 prosecutions – Under the existing Data Protection Act
A4E Theft of unencrypted laptop containing personal data Hertfordshire County Council Fax error - leading to disclosure of personal data London Borough of Ealing Theft of unencrypted laptop containing personal data. London Borough of Hounslow Theft of unencrypted laptop containing personal data. Andrew Jonathan Crossley (ACS Law) Personal data exposed following inadequate web-hosting London Borough of Croydon Personal data stolen from a public house Cheshire East Council Disclosure of personal data via email to unintended recipients Brighton & Sussex Hospitals NHS Trust Insecure disposal of hard drives containing personal data Prudential Inaccuracy of customer records Sony Infiltration of online network Nursing and Midwifery Council DVDs containing personal data lost DM Design Bedrooms Ltd Making unsolicited marketing calls Nationwide Energy Services Ltd Making unsolicited marketing calls Bank of Scotland Multiple faxes containing personal data sent to incorrect recipient Jala Transport Theft of unencrypted portable hard drive First Financial (UK) Limited Sending unsolicited direct marketing texts British Pregnancy Advice Service Hacker threatened to publish thousands of names of people Think W3 Limited Hacker obtained large number of credit & debit card details Direct Assist Ltd Making direct marketing calls to people without their consent The Money Shop The theft and loss of servers containing customer data. Pharmacy 2U Limited Sold details of more than 20,000 customers TalkTalk Telecom Group PLC SQL injection attack Royal & Sun Alliance Insurance PLC The theft of a hard drive containing customer data 3
Consent to Collect and use of Data - auditability and traceability Right Of Access to the Data and Electronic Data Portability between Data Controllers Right To Be Forgotten – retention and deletion Right to Rectification – amendment/correction Obfuscation of Non- Operational Data (non production/analytical environments) Data transferability restrictions between
- rganisations and
external Data Processors Demonstrable control, security and processes showing evidence of governance and compliance
The broad terms of reference (GDPR principles)
4
Trust & Integrity Retention Risk & Liabilities Access, Auditability Security & Control
Insecure and undefined access is by itself a time bomb ticking away within your organisation… The proliferation of personal data across your organisation has major implications for your IT department 90 % of data breaches occur in the “shadow data” environment. Risk and Liabilities Where the data is held and by whom and by what, in addition to the jurisdiction and possible remedial action 20 million pending civil cases in the Indian judicial system No organisation wants to collect personalised data that has not been derived without the consent
- f the individual
Collecting, managing and analysing erroneous, outdated personal data has major implications
5
GDPR is just the spotlight to address a series of interconnected problems
6
3 Distinct phases of activity
Interpretation - of the Regulations
This will be dictated by your appetite for risk & desire to mitigate that risk
- The complexity of your
- rganisation
- The type of data you hold &
how you hold it
Creation - of Policy and Process
- Privacy Notices & Consent
- Subject Access Requests
- Breach Notification
- Commercial and 3 Party
interests
- Big Data & Analytics
- Lawful Processing
- Legitimate Interest &
Direct marketing
- Data Retention/Erasure
Execution - applying policy and process
- DPIA - Impact Assessment
- Creation & maintenance
- f your
- Information Asset Register -
MDM
- Erasure & Purging/Obfuscation
- IS27001 - Cyber
- Essentials/Encryption
GDPR: What’s your next step?
7
1 2 3 4 Governance & Policy Process & Procedure People & Culture Technology Data Security
Dimensions
Dimensions
In Discovery – we will begin to baseline your ‘As-is’ across the 6 dimensions
- f GDPR compliance
We will isolate the key elements - policies, processes, technology, roles, responsibilities and more importantly- the context, complexity of what data you have and why you hold that personal data and what use you make of it.
8
9
In Analysis - we will work with you to conduct a systematic and thorough review of personal information processing and storage, within your organisation and operations Leveraging the Capita GDPR intellectual property; we will review your governance, policy and procedures that are associated with GDPR compliance:
- GDPR Information & Security Policy
- Information & Data Asset Register
- Products / Services Assessment
- Privacy Notices
- Subject Access Requests
- Breach Notification & Incident Management
- Data Retention & Erasure
- Commercial (3rd parties)
Define a plan data flow mapping Gap assessment Address data transfer & sub- contracting
10
In Recommendations we will:
- Produce a baseline of the current state, any known changes and identification
- f any discovered gaps assisting you in achieving compliance
- Highlight areas of concern from the Analysis phase
- Create a roadmap for your compliance journey
- Develop, Document and populate your compliance/risk management
environment using our GDPR Management Compliance Portal Example GDPR implementation plan
JAN MAR JUN SEP NOV DEC JAN FEB APR
2017 2018
DEADLINE
Data inventory Security data breach plan Right to be forgotten data portability Assess readiness Build a plan Identify DPO Build consensus Awareness training & SAR DPIA & consent mechanism Storage limitation