1
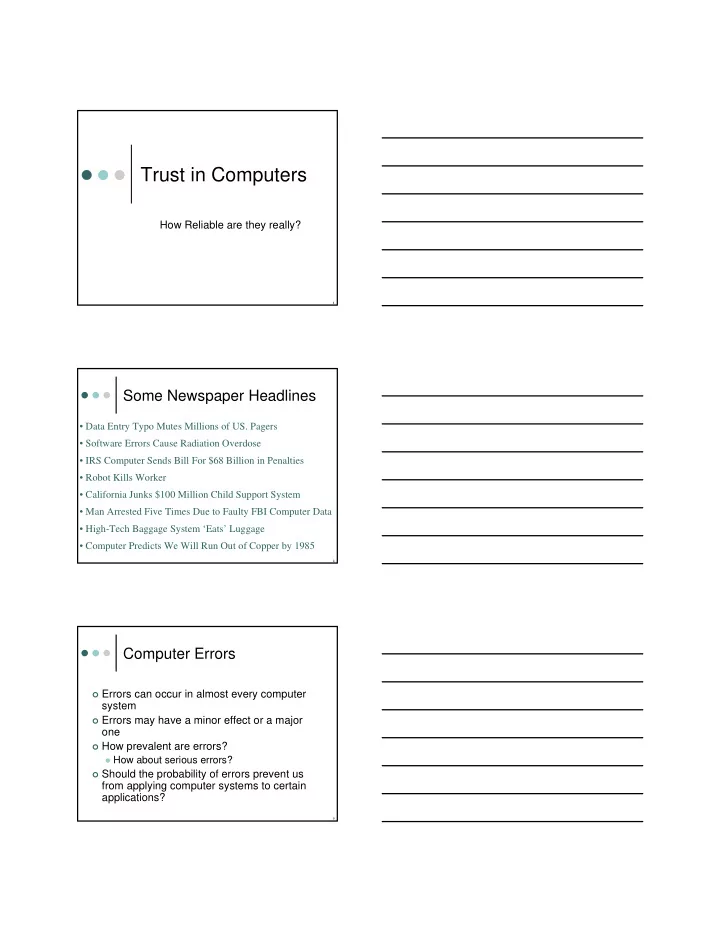
Trust in Computers
How Reliable are they really?
2
Some Newspaper Headlines
- Data Entry Typo Mutes Millions of US. Pagers
- Software Errors Cause Radiation Overdose
- IRS Computer Sends Bill For $68 Billion in Penalties
- Robot Kills Worker
- California Junks $100 Million Child Support System
- Man Arrested Five Times Due to Faulty FBI Computer Data
- High-Tech Baggage System ‘Eats’ Luggage
- Computer Predicts We Will Run Out of Copper by 1985
3
Computer Errors
Errors can occur in almost every computer
system
Errors may have a minor effect or a major
- ne
How prevalent are errors? How about serious errors? Should the probability of errors prevent us