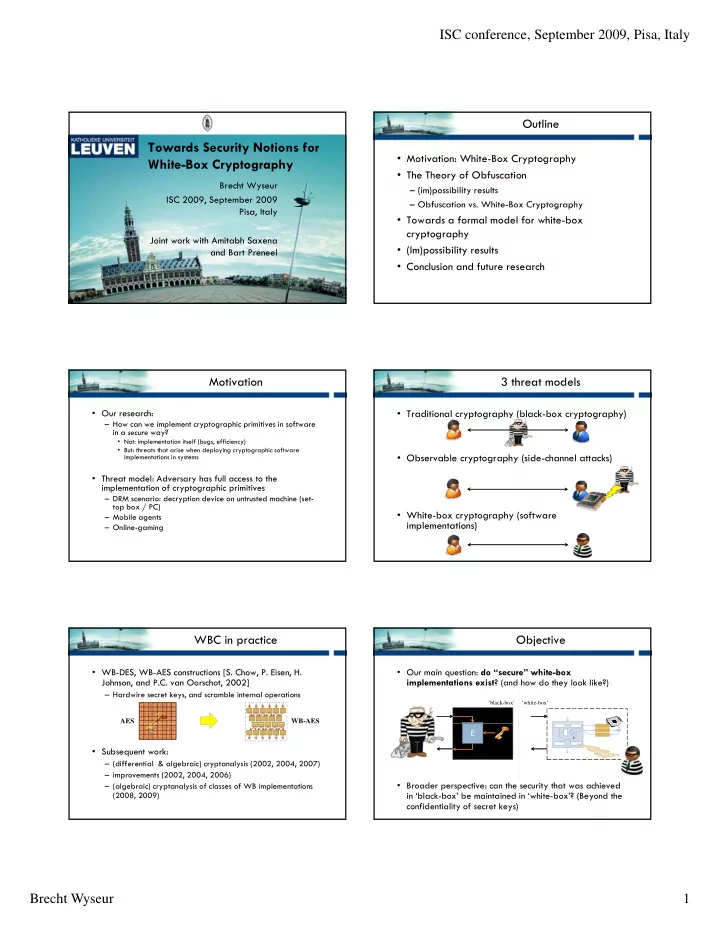
ISC conference, September 2009, Pisa, Italy Brecht Wyseur 1 Towards Security Notions for White-Box Cryptography
Brecht Wyseur ISC 2009, September 2009 Pisa, Italy Joint work with Amitabh Saxena and Bart Preneel
Outline
- Motivation: White-Box Cryptography
- The Theory of Obfuscation
– (im)possibility results – Obfuscation vs. White-Box Cryptography yp g p y
- Towards a formal model for white-box
cryptography
- (Im)possibility results
- Conclusion and future research
Motivation
- Our research:
– How can we implement cryptographic primitives in software in a secure way?
- Not: implementation itself (bugs, efficiency)
- But: threats that arise when deploying cryptographic software
implementations in systems
- Threat model: Adversary has full access to the
implementation of cryptographic primitives
– DRM scenario: decryption device on untrusted machine (set- top box / PC) – Mobile agents – Online-gaming
3 threat models
- Traditional cryptography (black-box cryptography)
- Observable cryptography (side-channel attacks)
- White-box cryptography (software
implementations)
WBC in practice
- WB-DES, WB-AES constructions [S. Chow, P. Eisen, H.
Johnson, and P.C. van Oorschot, 2002]
– Hardwire secret keys, and scramble internal operations
08 C1 EE 18 33 78 08 0F B6 C6 33 3C 85 80 50 14 95 80 4C 00 08 C1 E8 45 D8 C1 E9 10 0F B6 C9 C4 89 49 54 0F
AES WB-AES
- Subsequent work:
– (differential & algebraic) cryptanalysis (2002, 2004, 2007) – improvements (2002, 2004, 2006) – (algebraic) cryptanalysis of classes of WB implementations (2008, 2009)
4D C1 9C 8B 14 95 5D CC C1 E8 18 7D D0 85 D4 55 94 E3 6C 0F 8B 5D 1C 5F
Objective
- Our main question: do “secure” white-box
implementations exist? (and how do they look like?)
‘white-box’ ‘black-box’
- Broader perspective: can the security that was achieved
in ‘black-box’ be maintained in ‘white-box’? (Beyond the confidentiality of secret keys)
E
k