1
1
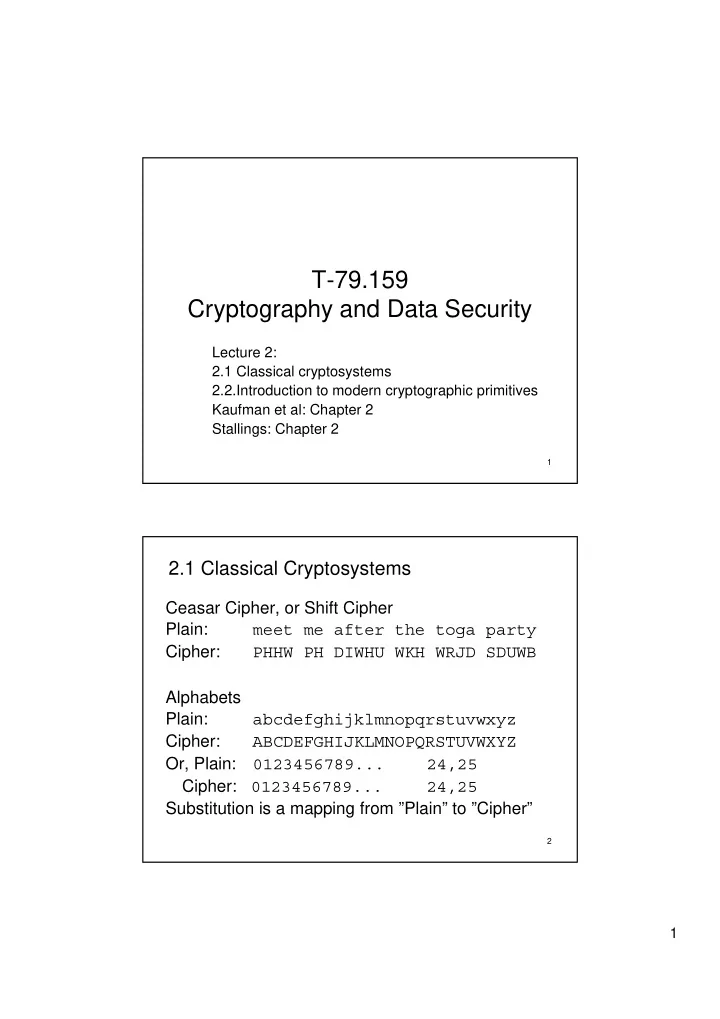
T-79.159 Cryptography and Data Security
Lecture 2: 2.1 Classical cryptosystems 2.2.Introduction to modern cryptographic primitives Kaufman et al: Chapter 2 Stallings: Chapter 2
2
T-79.159 Cryptography and Data Security Lecture 2: 2.1 Classical - - PDF document
T-79.159 Cryptography and Data Security Lecture 2: 2.1 Classical cryptosystems 2.2.Introduction to modern cryptographic primitives Kaufman et al: Chapter 2 Stallings: Chapter 2 1 2.1 Classical Cryptosystems Ceasar Cipher, or Shift Cipher
1
2
3
4
5
6
2.406 M 4.025 L 0.772 K 0.153 J 6.996 I 6.094 H 2.015 G 2.228 F 12.702 E 4.253 D 2.782 C 1.492 B 8.167 A 0.074 Z 1.974 Y 0.150 X 2.360 W 0.978 V 2.758 U 9.056 T 6.327 S 5.987 R 0.095 Q 1.929 P 7.507 O 6.749 N
7
8
16 M L 1 K 11 J 5 I 4 H 1 G 11 F 7 E 13 D 15 C 1 B A 20 Z 10 Y 6 X 8 W 5 V 5 U 2 T 3 S 10 R 4 Q 1 P O 9 N
9
10
11
12
13
14
15
16
17
18
19
20
Z X W V U T S Q P L K I/J G F E D B Y H C R A N O M Plaintext formatting
Regular case
Same row or column
21
22
23
24
25
26
27
28
Symmetric primitives are
Asymmetric (public key primitives) are
from infeasibility of som computationally hard problem.
Note: it would be possible to construct symmetric primitives based on mathematics, but they are not used in practise because they are not efficient compared to symmetric primitives
29
Confidentiality primitive
knowledge of the key.
Plaintext P: strings of bits of fixed length n Ciphertext C: strings of bits of the same length n Key K: string of bits of fixed length k Encryption transformations: For each fixed key the encryption operation EK is one-to-one (invertible) function from the set of plaintexts to the set of ciphertext. That is, there exist an inverse transformation, decryption transformation DK such that for each P and K we have: DK ( EK (P ) ) = P (Message , Secret key ) Ciphertext (Ciphertext, Secret key ) Message
30
31
– Substitution permutation network (SPN) – Feistel network
32
33
when implemented in hardware.
word by word, while block ciphers require buffering to accumulate the full plaintext block.
is done character by character with keys Ki that are independent of the data Ci = EKi(Pi )
sequence is complex
Ci = (Pi + Ki )mod 26
34
Secret key Key stream (Key stream , Message) Ciphertext Secret key Key stream (Ciphertext, Key stream ) Message
35
the same but nothing more.
self-synchronising stream cipher.
without knowing the key.
sequence allows also the keystream to be predicted with some
Requirements:
keystream for each key.
36
– Nonlinear combination generators: The keystream is generated as a nonlinear function of the outputs of multiple LFSRs – Nonlinear filter generators: The keystream is generated as a nonlinear function of stages of a single LFSR. – Clock controlled generators: In these constructions, the necessary nonlinearity is created by irregular clocking of the
stream cipher of this type.
37
function HK(P) of P under the control of a secret key K.
success probability larger than 1/2m. This is the probability of simply guessing the MAC value correctly at random. It should not be possible to increase this probability even if a large number of correct pairs P and HK(P) is available to the attacker. (Secret key , Message) MAC (Secret key , Message) MAC
38
relatively large blocks of data. Most MACs are iterated
compression function. At each round the compression function takes a new data block and compresses it together with the compression result from the previous rounds. Hence the length of the message to be authenticated determines how many iteration rounds are required to compute the MAC value.
anybody in possession of the secret key K and the MAC computation algorithm.
39
function H(P) of P . The hash length m is fixed.
that H(P) = h
such that H(P’) = H(P)
P ≠ P’ and H(P’) = H(P) Message Hash code Message Hash code
40
large blocks of data. Most hash functions are iterated
compression function. At each round the compression function takes a new data block and compresses it together with the compression result from the previous rounds. Hence the length of the message to be authenticated determines how many iteration rounds are required to compute the MAC value.
the hash code of P.
41
protocols than just bulk message encryption: authentication, key agreement etc.
rules (with hash functions) are required.
than chosen plaintext (for symmetric block ciphers they are about the same). We will see an example later.
(Message , Public key ) Ciphertext (Ciphertext , Private key ) Message
42
fixed length hash of the message.
– message authentication protocols – non-repudiation protocols – authentication and key agreement – commitment schemes – …
(Message , Private key ) Signature (Signature , Public key ) Validity (1 bit)