SLIDE 1
1
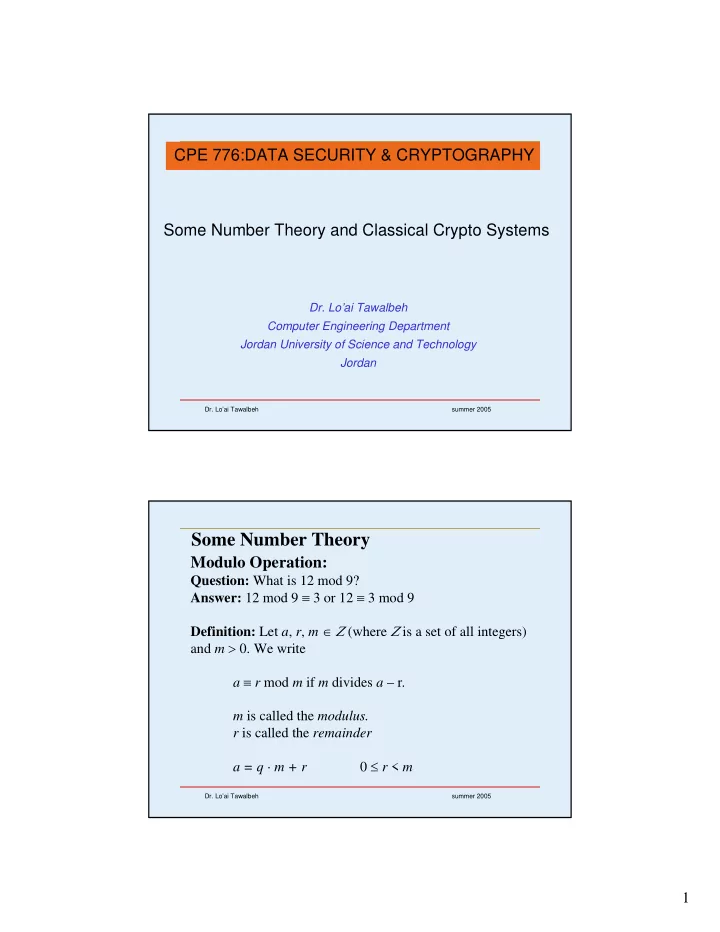
- Dr. Lo’ai Tawalbeh
summer 2005
Some Number Theory and Classical Crypto Systems
- Dr. Lo’ai Tawalbeh
Computer Engineering Department Jordan University of Science and Technology Jordan
CPE 776:DATA SECURITY & CRYPTOGRAPHY
- Dr. Lo’ai Tawalbeh
summer 2005