9/15/05 Jie Gao CSE590-fall05 1
Simulations of the quadrilateral Simulations of the quadrilateral-
- based
based localization localization
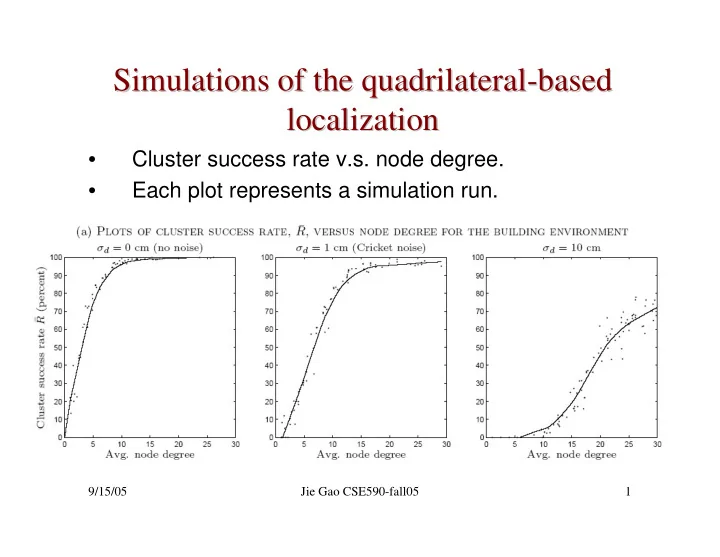
- Cluster success rate v.s. node degree.
- Each plot represents a simulation run.
Simulations of the quadrilateral- -based based Simulations of the - - PowerPoint PPT Presentation
Simulations of the quadrilateral- -based based Simulations of the quadrilateral localization localization Cluster success rate v.s. node degree. Each plot represents a simulation run. 9/15/05 Jie Gao CSE590-fall05 1 Random
9/15/05 Jie Gao CSE590-fall05 1
9/15/05 Jie Gao CSE590-fall05 2
9/15/05 Jie Gao CSE590-fall05 3
9/15/05 Jie Gao CSE590-fall05 4
9/15/05 Jie Gao CSE590-fall05 5
9/15/05 Jie Gao CSE590-fall05 6
Lemma: By local angles of a unit-disk graph, we can determine all pairs of crossing edges in a valid embedding.
If AB crosses CD in UDG, then by the crossing lemma, one of them, say B, has edges to the other three nodes.
9/15/05 Jie Gao CSE590-fall05 7
9/15/05 Jie Gao CSE590-fall05 8
9/15/05 Jie Gao CSE590-fall05 9
6 11
3 2
3 2
3 2
3 2 Consider a unit-disk graph, where the two ‘teeth’ do not cross:
9/15/05 Jie Gao CSE590-fall05 10
Consider a unit-disk graph, where the two ‘teeth’ do not cross: Case 1: Case 2:
6 11
3 2
3 2
3 2
3 2
6 11
3 2
3 2
3 2
3 2
9/15/05 Jie Gao CSE590-fall05 11
9/15/05 Jie Gao CSE590-fall05 12
Consider a unit-disk graph, where the two ‘teeth’ do not cross: Case 1: Case 2:
6 11
3 2
3 2
3 2
3 2
6 11
3 2
3 2
3 2
3 2
2 1 ≤
2 1 ≤
3 2 ≥
3 2 ≥
1
1=
1=
1=
1
1=
9/15/05 Jie Gao CSE590-fall05 13
9/15/05 Jie Gao CSE590-fall05 14
1=
1=
Case 1:
1=
1=
Case 2:
Use triangles to enforce that the teeth are large enough.
9/15/05 Jie Gao CSE590-fall05 15
9/15/05 Jie Gao CSE590-fall05 16
1
2
3
1
2
3
2 1 ≤
3 2 ≥
9/15/05 Jie Gao CSE590-fall05 17
9/15/05 Jie Gao CSE590-fall05 18
9/15/05 Jie Gao CSE590-fall05 19
Variables: lengths of edges, .
Each node’s position (x, y) is a linear function of the variables.
9/15/05 Jie Gao CSE590-fall05 20
Variables: lengths of edges, . Constraints: 1. Edge length constraint 2. Cycle constraint: for a cycle with edges 3. Unit disk graph property. For two nodes u, v without an edge, |uv|>1. Non-convex. So we can’t solve it.
9/15/05 Jie Gao CSE590-fall05 21
Variables: lengths of edges, . Relax the constraints: use as many linear constraints as possible: 1. Edge length constraint 2. Cycle constraint: for a cycle with edges
9/15/05 Jie Gao CSE590-fall05 22
Variables: lengths of edges, . Linear Constraints: 3. ∃edges AB, BC, and no AC 4. Crossing edge constraint:
A B C α for quasi-UDG
9/15/05 Jie Gao CSE590-fall05 23
The LP doesn’t necessarily produces a valid embedding, but it works well in practice. True Network (600 nodes) Embedding
9/15/05 Jie Gao CSE590-fall05 24
True Network (600 nodes) Embedding The LP doesn’t necessarily produces a valid embedding, but it works well in practice.
9/15/05 Jie Gao CSE590-fall05 25
Largest connected component
9/15/05 Jie Gao CSE590-fall05 26
True Network (225 nodes) Embedding
9/15/05 Jie Gao CSE590-fall05 27
9/15/05 Jie Gao CSE590-fall05 28
9/15/05 Jie Gao CSE590-fall05 29
– Multipath, shadowing, sensor imperfections, changes in propagation properties and more
– Many formulations of localization problems, how do you solve the
– How do you solve the problem in a distributed manner, under computation and storage constraints?
– Nodes have to collaborate and communicate to solve the problem – If you are using it for routing, it means you don’t have routing support to solve the problem! How do you do it?
– How do you build a whole system for localization? – How do you integrate location services with other applications? – Different implementation for each setup, sensor, integration issue
9/15/05 Jie Gao CSE590-fall05 30
Computer Science Department Stony Brook University
9/15/05 Jie Gao CSE590-fall05 31
with guaranteed delivery in ad hoc wireless networks, Wireless Networks, 7(6), 609-616, 2001.
Routing for Wireless Networks, in MobiCom 2000.
9/15/05 Jie Gao CSE590-fall05 32
information between pairs of nodes wishing to communicate.
each node that is updated as changes in the network topology are detected.
global routing table is maintained.
are more appropriate for ad hoc networks.
– Ad hoc on demand distance vector routing (AODV) – Dynamic source routing (DSR)
9/15/05 Jie Gao CSE590-fall05 33
attributes and sensed data, rather than on pre-assigned network address.
to that route.
– Nodes know their geographical location – Nodes know their 1-hop neighbors – Routing destinations are specified geographically (a location, or a geographical region) – Each packet can hold a small amount (O(1)) of routing information. – The connectivity graph is modeled as a unit disk graph.
9/15/05 Jie Gao CSE590-fall05 34
– The location of the destination node; – The location of itself and its 1-hop neighbors.
– No flooding is involved.
– The one closest to the destination in Euclidean distance. – The one with smallest angle towards the destination: “compass routing”. – Etc.
9/15/05 Jie Gao CSE590-fall05 35
9/15/05 Jie Gao CSE590-fall05 36
t s t
s
Send packets to the neighbor closest to the destination
9/15/05 Jie Gao CSE590-fall05 37
Send packets to the neighbor with smallest angle towards the destination
9/15/05 Jie Gao CSE590-fall05 38
9/15/05 Jie Gao CSE590-fall05 39
connecting source to destination.
9/15/05 Jie Gao CSE590-fall05 40
9/15/05 Jie Gao CSE590-fall05 41
9/15/05 Jie Gao CSE590-fall05 42
9/15/05 Jie Gao CSE590-fall05 43
9/15/05 Jie Gao CSE590-fall05 44
9/15/05 Jie Gao CSE590-fall05 45
9/15/05 Jie Gao CSE590-fall05 46
9/15/05 Jie Gao CSE590-fall05 47
– Source and destination positions – The node when it enters the perimeter mode. – The first edge on the current face.
– Knowledge about direct neighbors’ positions is sufficient – Faces are implicit. Only local neighbor ordering around each node is needed
“Right Hand Rule”
9/15/05 Jie Gao CSE590-fall05 48
9/15/05 Jie Gao CSE590-fall05 49
– Preserves connectivity. – Distributed computation.
9/15/05 Jie Gao CSE590-fall05 50
9/15/05 Jie Gao CSE590-fall05 51
9/15/05 Jie Gao CSE590-fall05 52
9/15/05 Jie Gao CSE590-fall05 53
9/15/05 Jie Gao CSE590-fall05 54
9/15/05 Jie Gao CSE590-fall05 55
9/15/05 Jie Gao CSE590-fall05 56
9/15/05 Jie Gao CSE590-fall05 57
9/15/05 Jie Gao CSE590-fall05 58
9/15/05 Jie Gao CSE590-fall05 59
9/15/05 Jie Gao CSE590-fall05 60
9/15/05 Jie Gao CSE590-fall05 61
200 nodes randomly deployed in a 2000×2000 meters region. Radio range =250meters
9/15/05 Jie Gao CSE590-fall05 62
9/15/05 Jie Gao CSE590-fall05 63