Introduction Description Security Implementation
SIMD Is a Message Digest
Gaëtan Leurent, Pierre-Alain Fouque, Charles Bouillaguet
École Normale Supérieure Paris, France http://www.di.ens.fr/~leurent/simd.html
First SHA-3 Conference
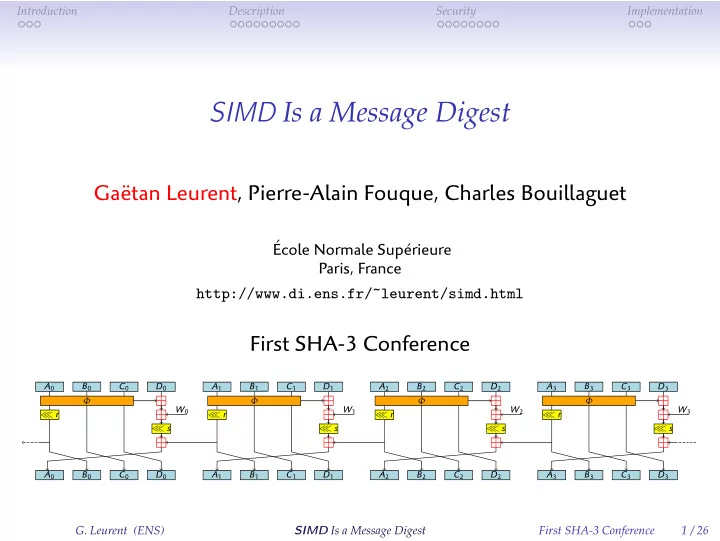
A0 B0 W0 C0 D0 D0 A0 B0 C0 ≪ r Φ ≪ s A1 B1 W1 C1 D1 D1 A1 B1 C1 ≪ r Φ ≪ s A2 B2 W2 C2 D2 D2 A2 B2 C2 ≪ r Φ ≪ s A3 B3 W3 C3 D3 D3 A3 B3 C3 ≪ r Φ ≪ s
- G. Leurent (ENS)
SIMD Is a Message Digest First SHA-3 Conference 1 / 26