SLIDE 1
1
1
Requirements for IPsec Negotiation in the SIP Framework
August 1, 2005 Makoto Saito (ma.saito@ntt.com) Shingo Fujimoto (shingo_fujimoto@jp.fujitsu.com)
draft-saito-mmusic-ipsec-negotiation-req-00.txt
2
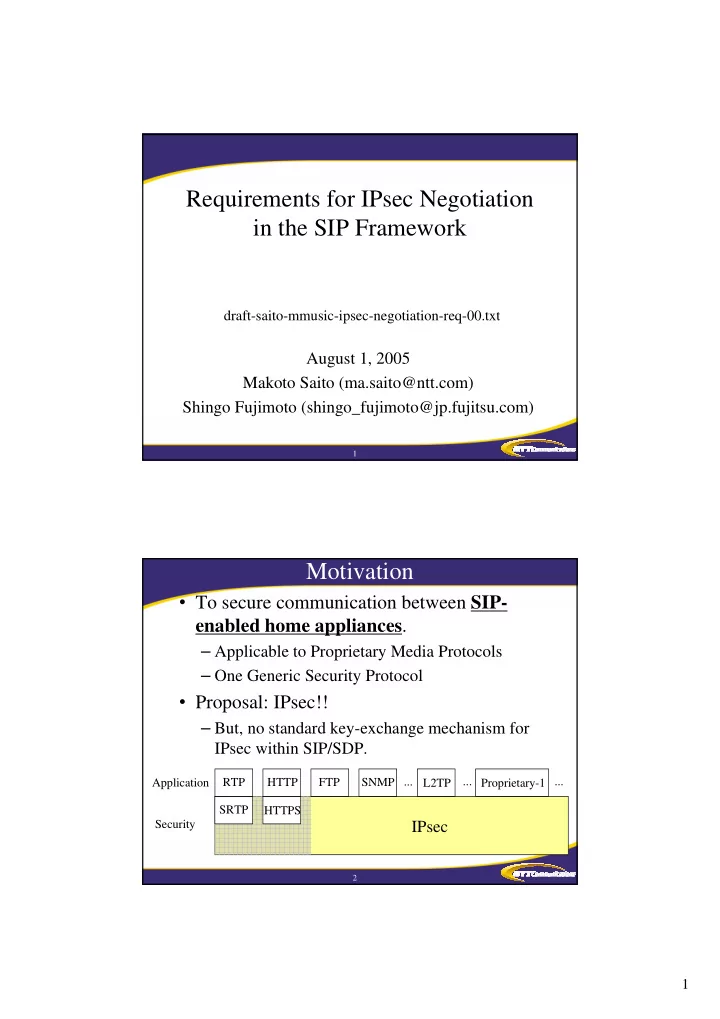
- To secure communication between SIP-
enabled home appliances.
– Applicable to Proprietary Media Protocols – One Generic Security Protocol
- Proposal: IPsec!!
– But, no standard key-exchange mechanism for IPsec within SIP/SDP.
Motivation
SRTP RTP HTTP HTTPS SNMP FTP ... L2TP Proprietary-1 ... ...
IPsec
Application Security