9/ 29/ 2009 | 1 2009 Fall Peng Liang Requirements Engineering
› Department of Computer Science / Peng Liang › Rijksuniversiteit Groningen (RUG)
› http:/ / www.cs.rug.nl/ ~liangp/ teaching/ courses/ RE2009Fall/
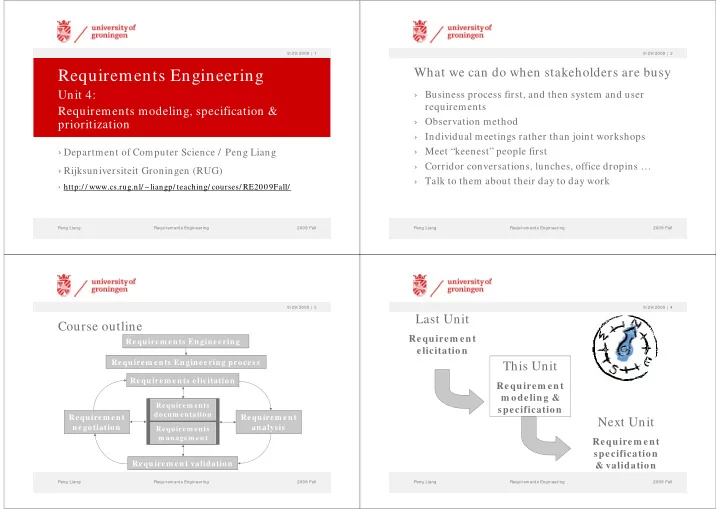
Requirements Engineering
Unit 4: Requirements modeling, specification & prioritization
2009 Fall | 2 Peng Liang Requirements Engineering 9/ 29/ 2009
What we can do when stakeholders are busy
› Business process first, and then system and user requirements › Observation method › Individual meetings rather than joint workshops › Meet “keenest” people first › Corridor conversations, lunches, office dropins … › Talk to them about their day to day work
2009 Fall | 3 Peng Liang Requirements Engineering 9/ 29/ 2009
Course outline
Requirem ents Engineering Requirem ents Engineering process Requirem ents elicitation Requirem ent analysis Requirem ent validation
Requirem ents docum entation
Requirem ent negotiation
Requirem ents m anagem ent
2009 Fall | 4 Peng Liang Requirements Engineering 9/ 29/ 2009