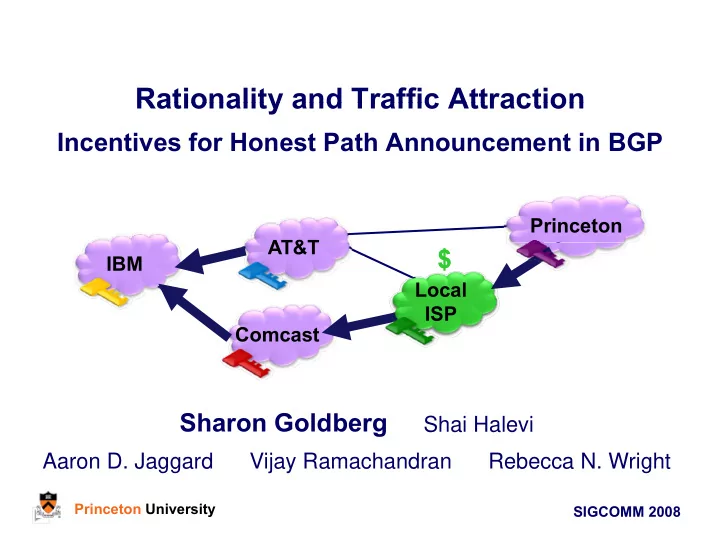
Rationality and Traffic Attraction Rationality and Traffic Attraction
Incentives for Honest Path Announcement in BGP
AT&T Princeton IBM AT&T Local ISP Local ISP
$
Comcast ISP ISP
Sharon Goldberg
Shai Halevi A D J d Vij R h d R b N W i h
Princeton University SIGCOMM 2008 Princeton University