1
Complex Adaptive Systems
C.d.L. Informatica – Università di Bologna
Peer-to-peer systems and
- verlay networks
Fabio Picconi Dipartimento di Scienze dell’Informazione 2
- Introduction to P2P systems
- Common topologies
- Data location
- Churn
- Newscast algorithm
- Security
Outline
3
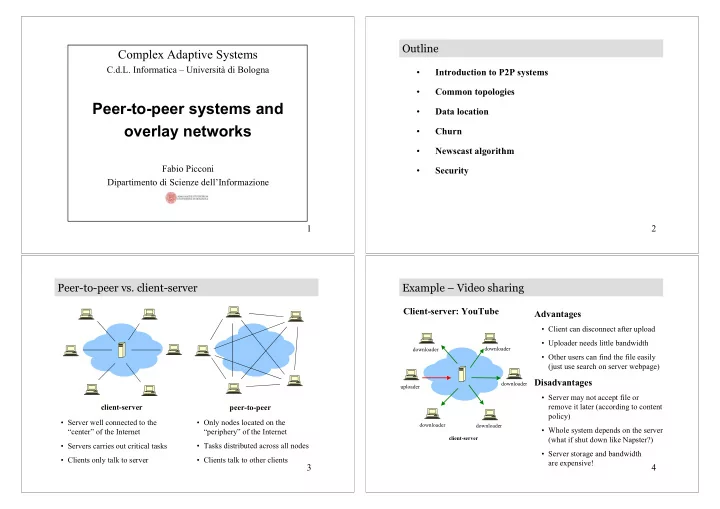
Peer-to-peer vs. client-server
client-server
- Server well connected to the
“center” of the Internet
- Servers carries out critical tasks
- Clients only talk to server
- Only nodes located on the
“periphery” of the Internet
- Tasks distributed across all nodes
- Clients talk to other clients
peer-to-peer
4
Example – Video sharing
Client-server: YouTube
client-server
Advantages
- Client can disconnect after upload
- Uploader needs little bandwidth
- Other users can find the file easily
(just use search on server webpage)
Disadvantages
- Server may not accept file or
remove it later (according to content policy)
- Whole system depends on the server
(what if shut down like Napster?)
- Server storage and bandwidth
are expensive!
uploader downloader downloader downloader downloader downloader