SLIDE 1
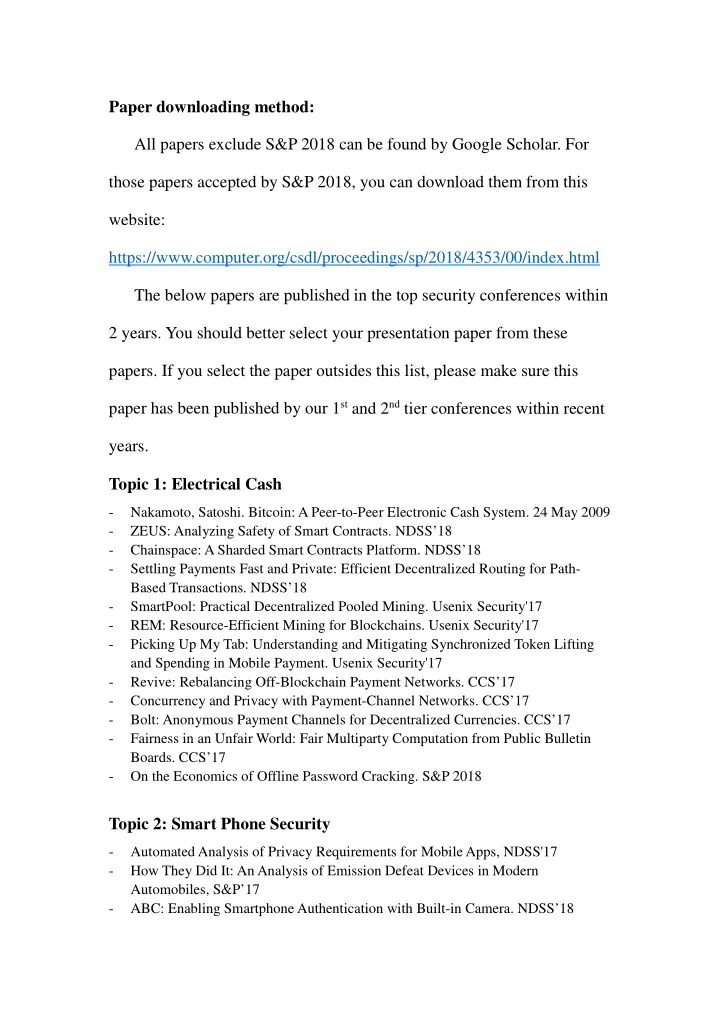
Paper downloading method: All papers exclude S&P 2018 can be found by Google Scholar. For those papers accepted by S&P 2018, you can download them from this website: https://www.computer.org/csdl/proceedings/sp/2018/4353/00/index.html The below papers are published in the top security conferences within 2 years. You should better select your presentation paper from these
- papers. If you select the paper outsides this list, please make sure this
paper has been published by our 1st and 2nd tier conferences within recent years. Topic 1: Electrical Cash
- Nakamoto, Satoshi. Bitcoin: A Peer-to-Peer Electronic Cash System. 24 May 2009
- ZEUS: Analyzing Safety of Smart Contracts. NDSS’18
- Chainspace: A Sharded Smart Contracts Platform. NDSS’18
- Settling Payments Fast and Private: Efficient Decentralized Routing for Path-
Based Transactions. NDSS’18
- SmartPool: Practical Decentralized Pooled Mining. Usenix Security'17
- REM: Resource-Efficient Mining for Blockchains. Usenix Security'17
- Picking Up My Tab: Understanding and Mitigating Synchronized Token Lifting
and Spending in Mobile Payment. Usenix Security'17
- Revive: Rebalancing Off-Blockchain Payment Networks. CCS’17
- Concurrency and Privacy with Payment-Channel Networks. CCS’17
- Bolt: Anonymous Payment Channels for Decentralized Currencies. CCS’17
- Fairness in an Unfair World: Fair Multiparty Computation from Public Bulletin
- Boards. CCS’17
- On the Economics of Offline Password Cracking. S&P 2018
Topic 2: Smart Phone Security
- Automated Analysis of Privacy Requirements for Mobile Apps, NDSS'17
- How They Did It: An Analysis of Emission Defeat Devices in Modern
Automobiles, S&P’17
- ABC: Enabling Smartphone Authentication with Built-in Camera. NDSS’18