SLIDE 1
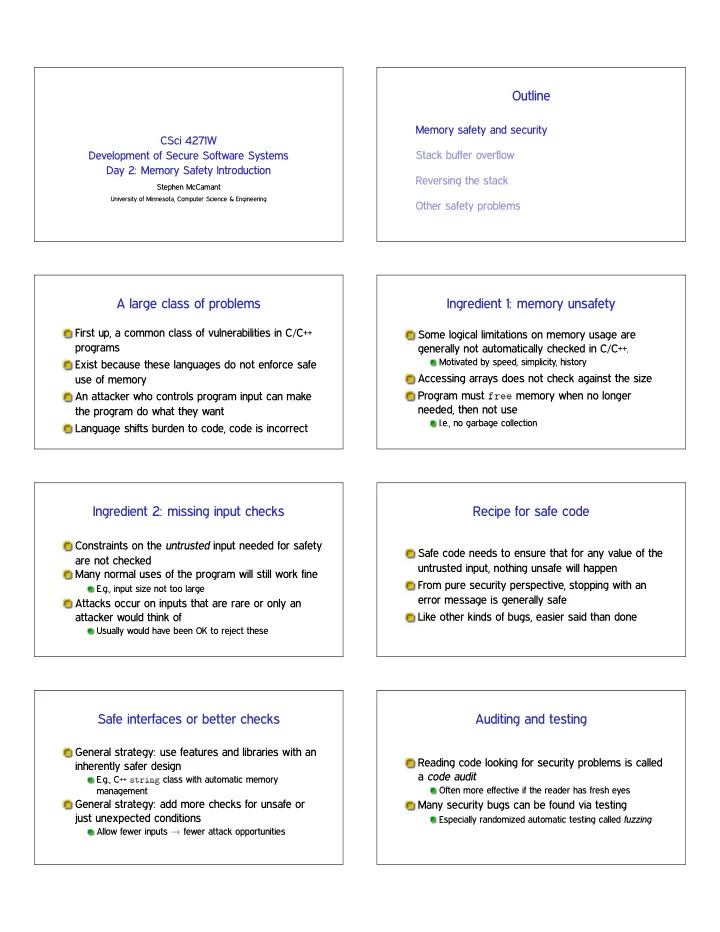
CSci 4271W Development of Secure Software Systems Day 2: Memory Safety Introduction
Stephen McCamant
University of Minnesota, Computer Science & Engineering
Outline Memory safety and security CSci 4271W Stack buffer - - PDF document
Outline Memory safety and security CSci 4271W Stack buffer overflow Development of Secure Software Systems Day 2: Memory Safety Introduction Reversing the stack Stephen McCamant University of Minnesota, Computer Science & Engineering
University of Minnesota, Computer Science & Engineering