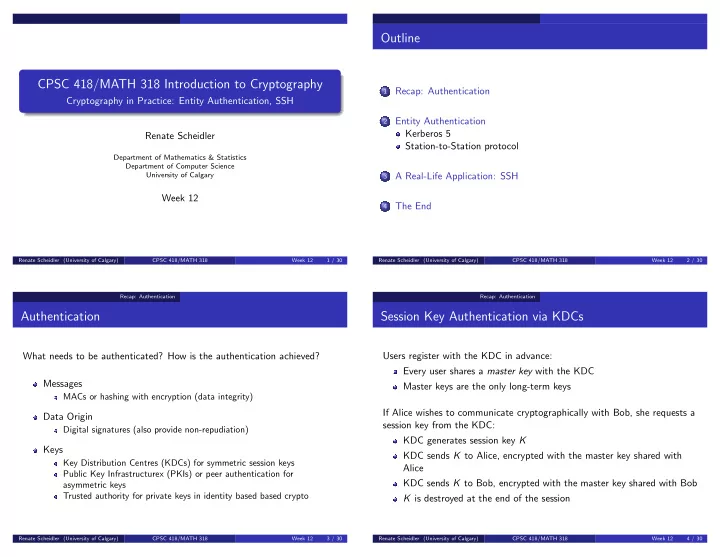
CPSC 418/MATH 318 Introduction to Cryptography
Cryptography in Practice: Entity Authentication, SSH Renate Scheidler
Department of Mathematics & Statistics Department of Computer Science University of Calgary
Week 12
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 12 1 / 30
Outline
1
Recap: Authentication
2
Entity Authentication Kerberos 5 Station-to-Station protocol
3
A Real-Life Application: SSH
4
The End
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 12 2 / 30 Recap: Authentication
Authentication
What needs to be authenticated? How is the authentication achieved? Messages
MACs or hashing with encryption (data integrity)
Data Origin
Digital signatures (also provide non-repudiation)
Keys
Key Distribution Centres (KDCs) for symmetric session keys Public Key Infrastructurex (PKIs) or peer authentication for asymmetric keys Trusted authority for private keys in identity based based crypto
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 12 3 / 30 Recap: Authentication
Session Key Authentication via KDCs
Users register with the KDC in advance: Every user shares a master key with the KDC Master keys are the only long-term keys If Alice wishes to communicate cryptographically with Bob, she requests a session key from the KDC: KDC generates session key K KDC sends K to Alice, encrypted with the master key shared with Alice KDC sends K to Bob, encrypted with the master key shared with Bob K is destroyed at the end of the session
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 12 4 / 30