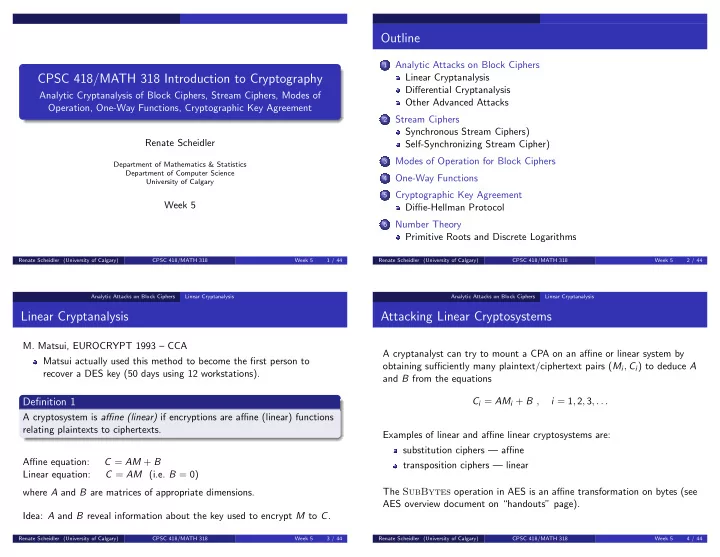
CPSC 418/MATH 318 Introduction to Cryptography
Analytic Cryptanalysis of Block Ciphers, Stream Ciphers, Modes of Operation, One-Way Functions, Cryptographic Key Agreement Renate Scheidler
Department of Mathematics & Statistics Department of Computer Science University of Calgary
Week 5
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 5 1 / 44
Outline
1
Analytic Attacks on Block Ciphers Linear Cryptanalysis Differential Cryptanalysis Other Advanced Attacks
2
Stream Ciphers Synchronous Stream Ciphers) Self-Synchronizing Stream Cipher)
3
Modes of Operation for Block Ciphers
4
One-Way Functions
5
Cryptographic Key Agreement Diffie-Hellman Protocol
6
Number Theory Primitive Roots and Discrete Logarithms
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 5 2 / 44 Analytic Attacks on Block Ciphers Linear Cryptanalysis
Linear Cryptanalysis
- M. Matsui, EUROCRYPT 1993 – CCA
Matsui actually used this method to become the first person to recover a DES key (50 days using 12 workstations).
Definition 1
A cryptosystem is affine (linear) if encryptions are affine (linear) functions relating plaintexts to ciphertexts. Affine equation: C = AM + B Linear equation: C = AM (i.e. B = 0) where A and B are matrices of appropriate dimensions. Idea: A and B reveal information about the key used to encrypt M to C.
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 5 3 / 44 Analytic Attacks on Block Ciphers Linear Cryptanalysis
Attacking Linear Cryptosystems
A cryptanalyst can try to mount a CPA on an affine or linear system by
- btaining sufficiently many plaintext/ciphertext pairs (Mi, Ci) to deduce A
and B from the equations Ci = AMi + B , i = 1, 2, 3, . . . Examples of linear and affine linear cryptosystems are: substitution ciphers — affine transposition ciphers — linear The SubBytes operation in AES is an affine transformation on bytes (see AES overview document on “handouts” page).
Renate Scheidler (University of Calgary) CPSC 418/MATH 318 Week 5 4 / 44