Networking Attacks: Link-, IP-, and TCP-layer attacks CS 161: - PowerPoint PPT Presentation
Networking Attacks: Link-, IP-, and TCP-layer attacks CS 161: Computer Security Prof. David Wagner February 28, 2013 General Communication Security Goals: CIA Confidentiality: No one can read our data / communication unless we want
Networking Attacks: Link-, IP-, and TCP-layer attacks CS 161: Computer Security Prof. David Wagner February 28, 2013
� General Communication Security Goals: CIA • Confidentiality: – No one can read our data / communication unless we want them to • Integrity – No one can manipulate our data / processing / communication unless we want them to • Availability – We can access our data / conduct our processing / use our communication capabilities when we want to • Also: no additional traffic other than ours … 2
Link-layer threats � • Confidentiality: eavesdropping (aka sniffing) • Integrity: injection of spoofed packets • Injection: delete legit packets (e.g., jamming) 3
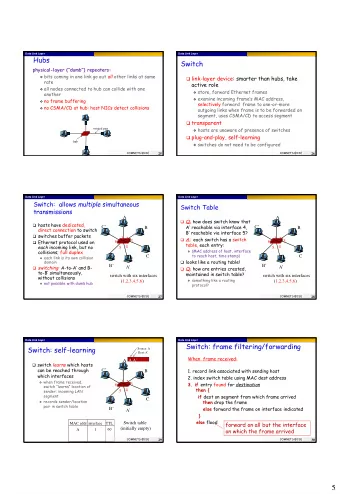
Layers 1 & 2: General Threats? � Framing and transmission of a collection of bits into individual messages sent across a 7 Application single “ subnetwork ” (one physical technology) 4 Transport 3 (Inter)Network 2 Link Encoding bits to send them over a single physical link 1 Physical e.g. patterns of voltage levels / photon intensities / RF modulation 4
� Eavesdropping • For subnets using broadcast technologies (e.g., WiFi, some types of Ethernet), get it for “ free ” – Each attached system’s NIC (= Network Interface Card) can capture any communication on the subnet – Some handy tools for doing so o tcpdump / windump (low-level ASCII printout) o Wireshark (GUI for displaying 800+ protocols) 5
� TCPDUMP: Packet Capture & ASCII Dumper 6
� Wireshark: GUI for Packet Capture/Exam. 7
� Wireshark: GUI for Packet Capture/Exam. 8
� Wireshark: GUI for Packet Capture/Exam. 9
Stealing Photons � 10
11
� Link-Layer Threat: Disruption • If attacker sees a packet he doesn’t like, he can jam it (integrity) • Attacker can also overwhelm its signaling, e.g., jam WiFi’s RF (denial-of-service) 12
� Link-Layer Threat: Disruption • If attacker sees a packet he doesn’t like, he can jam it (integrity) • Attacker can also overwhelm its signaling, e.g., jam WiFi’s RF (denial-of-service) • There’s also the heavy-handed approach … 13
14
� Link-Layer Threat: Spoofing • Attacker can inject spoofed packets, and lie about the source address M D C Hello world! 15
� Physical/Link-Layer Threats: Spoofing • With physical access to a subnetwork, attacker can create any message they like – When with a bogus source address: spoofing • When using a typical computer, may require root/administrator to have full freedom • Particularly powerful when combined with eavesdropping – Because attacker can understand exact state of victim’s communication and craft their spoofed traffic to match it – Spoofing w/o eavesdropping = blind spoofing 16
On-path vs Off-path Spoofing � Host A communicates with Host D Host C Host D Host A Router 1 Router 2 Router 3 On-path Router 5 Host B Host E Router 7 Router 6 Router 4 Off-path 17
� Spoofing on the Internet • On-path attackers can see victim’s traffic ⇒ spoofing is easy • Off-path attackers can’t see victim’s traffic – They have to resort to blind spoofing – Often must guess/infer header values to succeed o We then care about work factor: how hard is this – But sometimes they can just brute force o E.g., 16-bit value: just try all 65,536 possibilities! • When we say an attacker “ can spoof ” , we usually mean “ w/ reasonable chance of success ” 18
Layer 3: General Threats? � Bridges multiple “ subnets ” to 7 Application provide end-to-end internet 4 Transport connectivity between nodes 3 (Inter)Network 4-bit 8-bit 2 Link 4-bit 16-bit Total Length (Bytes) Header Type of Service Version Length (TOS) 1 Physical 3-bit 13-bit Fragment Offset 16-bit Identification Flags 8-bit Time to 8-bit Protocol 16-bit Header Checksum Live (TTL) 32-bit Source IP Address 32-bit Destination IP Address IP = Internet Protocol Payload 19
� IP-Layer Threats • Can set arbitrary source address – “ Spoofing ” - receiver has no idea who you are – Could be blind, or could be coupled w/ sniffing – Note: many attacks require two-way communication o So successful off-path/blind spoofing might not suffice • Can set arbitrary destination address – Enables “ scanning ” - brute force searching for hosts • Can send like crazy (flooding) – IP has no general mechanism for tracking overuse – IP has no general mechanism for tracking consent – Very hard to tell where a spoofed flood comes from! • If attacker can manipulate routing, can bring traffic to themselves for eavesdropping (not easy) 20
LAN Bootstrapping: DHCP � • New host doesn’t have an IP address yet – So, host doesn’t know what source address to use • Host doesn’t know who to ask for an IP address – So, host doesn’t know what destination address to use • Solution: shout to “ discover ” server that can help – Broadcast a server-discovery message (layer 2) – Server(s) sends a reply offering an address ... � host � host � host � DHCP server � 21
Dynamic Host Configuration Protocol � DHCP discover � (broadcast) � � r e f f DHCP server � o P C new H D client � “ offer ” message includes IP address, DHCP request � DNS server, “ gateway router ” , and how long (broadcast) � client can have these ( “ lease ” time) � K C A P C H D 22
Dynamic Host Configuration Protocol � DHCP discover � (broadcast) � � r e f f DHCP server � o P C new H D client � “ offer ” message includes IP address, DHCP request � DNS server, “ gateway router ” , and how long (broadcast) � client can have these ( “ lease ” time) Threats? � K C A P C H D 23
Dynamic Host Configuration Protocol � DHCP discover � (broadcast) � � r e f f DHCP server � o P C new H D client � “ offer ” message includes IP address, DHCP request � DNS server, “ gateway router ” , and how long (broadcast) � Attacker on same client can have these subnet can hear ( “ lease ” time) new host’s DHCP request � K C A P C H D 24
Dynamic Host Configuration Protocol � DHCP discover � (broadcast) � � r e f f DHCP server � o P C new H D client � “ offer ” message includes IP address, DHCP request � DNS server, “ gateway router ” , and how long (broadcast) � client can have these ( “ lease ” time) � K C A P C H Attacker can race the actual D server; if they win, replace DNS server and/or gateway router 25
� DHCP Threats • Substitute a fake DNS server – Redirect any of a host’s lookups to a machine of attacker’s choice • Substitute a fake gateway router – Intercept all of a host’s off-subnet traffic o (even if not preceded by a DNS lookup) – Relay contents back and forth between host and remote server and modify however attacker chooses • An invisible Man In The Middle (MITM) – Victim host has no way of knowing it’s happening o (Can’t necessarily alarm on peculiarity of receiving multiple DHCP replies, since that can happen benignly) • How can we fix this? Hard 26
TCP � 7 Application 4 Transport 3 (Inter)Network Source port Destination port 2 Link Sequence number 1 Physical Acknowledgment HdrLen Advertised window Flags 0 Checksum Urgent pointer Options (variable) Data 27
TCP � 7 Application These plus IP addresses define a given connection 4 Transport 3 (Inter)Network Source port Destination port 2 Link Sequence number 1 Physical Acknowledgment HdrLen Advertised window Flags 0 Checksum Urgent pointer Options (variable) Data 28
TCP � 7 Application Defines where this packet fits within the 4 Transport sender’s bytestream 3 (Inter)Network Source port Destination port 2 Link Sequence number 1 Physical Acknowledgment HdrLen Advertised window Flags 0 Checksum Urgent pointer Options (variable) Data 29
TCP Conn. Setup & Data Exchange � Client (initiator) Server IP address 1.2.1.2, port 3344 IP address 9.8.7.6, port 80 S r c A = 1 . 2 . 1 . 2 , S r c D P s = 3 t A 3 = 4 9 4 . 8 , . 7 . 6 , D s t P = 8 0 , S Y N , S e q = x SrcA=9.8.7.6, SrcP=80, DstA=1.2.1.2, DstP=3344, SYN+ACK, Seq = y, Ack = x+1 S r c A = 1 . 2 . 1 D . 2 s , t A S = r 9 c P . 8 = . 3 7 . 3 6 4 , D 4 , s t P = 8 0 , A C K , S e q = x + 1 , A c k = y + 1 S r c A = 1 . 2 . 1 . 2 , S r c P = 3 3 A 4 C 4 , D K s , S t e A q = = 9 . x 8 + . 7 1 , . 6 A , c D k s = t P y = + 8 1 0 , , D a t a = “ “ G E T / l o g i n . h t m l SrcA=9.8.7.6, SrcP=80, DstA=1.2.1.2, DstP=3344, ACK, Seq = y+1, Ack = x+16, Data= “ 200 OK … <html> … ” 30
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.




![Study 105 Atazanavir + [Cobicistat or Ritonavir] + TDF-FTC (Phase 2) Study 105: Study Design](https://c.sambuz.com/757054/study-105-s.webp)